2invoice: 0m Records Allegedly Leaked
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
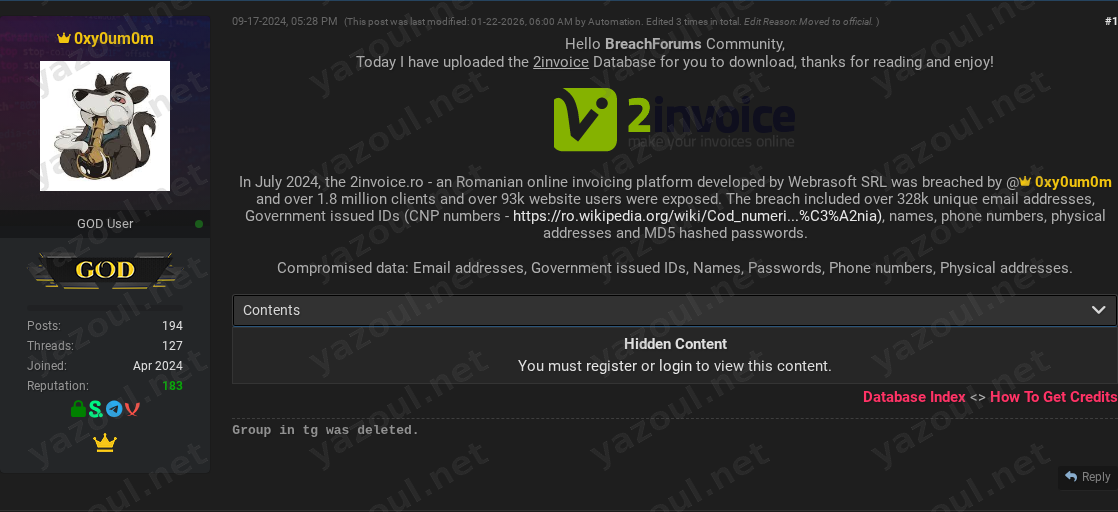
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
An actor using the alias “0xy0um0m” has posted an unverified claim on a dark web forum, alleging a significant data breach of 2invoice.ro, an online invoicing platform based in Romania. According to the post, the breach purportedly occurred in July 2024 and resulted in the exposure of data belonging to over 1.8 million clients and website users. The threat actor claims to have made the full database available for download on the forum, providing a file hash and size details. The post was originally made in September 2024 but shows a recent administrative edit in January 2026, suggesting ongoing forum activity around this dataset.
What Is Allegedly Exposed
The compromised data, as claimed by the actor, is described as extensive and sensitive. Allegedly exposed information includes over 328,000 unique email addresses, names, phone numbers, and physical addresses. Most critically, the post claims the leak includes government-issued identification numbers, specifically referencing Romanian CNP (Cod Numeric Personal) numbers, which are unique personal numeric codes. The actor also states that user passwords were exposed, though they were purportedly hashed using the MD5 algorithm, a dated and cryptographically weak hashing function. The total volume of records is claimed to be 1,836,864.
Threat Actor Profile
The post is authored by “0xy0um0m,” who claims responsibility for the breach. There is no widely recognized reputation or history associated with this alias in public cybersecurity reporting, marking them as an unknown actor. The post credits this same alias within its text, suggesting a sole operator. The lack of an established track record is a significant red flag, as new or unknown actors sometimes exaggerate claims or repackage old data to gain credibility within hacking communities. The specificity of the file hash (MD5: 08697BC33F2A2A3270FF0A23F189D1B5) and data sizes is a common tactic used to lend an air of legitimacy to such posts.
Potential Impact
If the claims are valid, the potential impact on affected individuals and the targeted organization, Webrasoft SRL, is severe. The alleged exposure of Romanian CNP numbers is particularly concerning, as this identifier is used extensively for official purposes and could facilitate identity theft, targeted phishing, and financial fraud. Combined with physical addresses, phone numbers, and weakly hashed passwords, the dataset could enable highly convincing social engineering attacks. For the business, such a breach could lead to significant regulatory scrutiny under laws like the GDPR, substantial financial penalties, and a severe loss of trust from its user base.
What to Watch For
- Organizational Response: Monitor for any official statement or breach notification from 2invoice.ro or its developer, Webrasoft SRL.
- Data Validation: Watch for other threat actors or researchers to comment on the legitimacy of the leaked data, or for the alleged dataset to appear on other leak sites.
- Credential Stuffing Campaigns: Given the claimed inclusion of email and password data, there is a risk of credential stuffing attacks against users who reused their 2Invoice password on other services.
- Targeted Phishing: Be alert for an increase in sophisticated, Romanian-language phishing attempts that leverage the alleged personal and identification data.
- Actor Activity: Note if the alias “0xy0um0m” posts further breaches or gains notoriety, which could retrospectively influence the assessment of this claim’s credibility.
Disclaimer
This report details an unverified claim from a dark web forum. Yazoul Security has not independently confirmed the breach of 2invoice.ro or the validity of the data described. The details presented, including the scale of the breach, the data types involved, and the threat actor’s role, are solely based on the forum post and must be treated as alleged. The provided file hash does not constitute proof of a genuine, unique breach, as hashes can be reused or falsified. Organizations and individuals should await confirmation from official sources before taking definitive action.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
Mag. Fünder Hausverwaltungs GmbH — incransom
Clearwater Marine Aquarium — qilin
Gruppo ICM SPA — qilin
Limkon — qilin