Iron March: 1186 records Records Allegedly Leaked
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
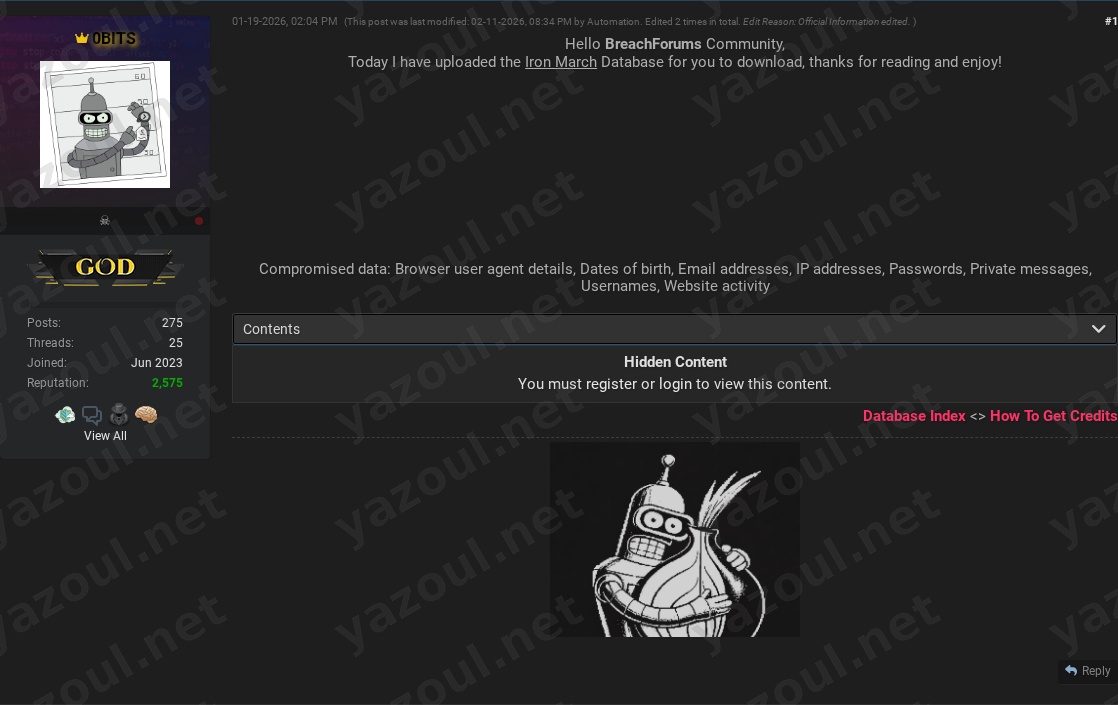
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
An actor using the alias “0BITS” has posted on a dark web forum, claiming to have leaked the complete database for the online forum known as Iron March. According to the unverified post, the leak contains 1,186 user records. The actor provided a compressed file size and an MD5 hash (C77B413D5882201232EA6610BD8E4A4C) for the alleged data dump, which they state includes sensitive personal information and private communications. The post, which was reportedly last edited by an automated process in February 2026, frames the leak as a share for the forum community.
What Is Allegedly Exposed
The threat actor claims the compromised database contains a wide array of sensitive user data. Allegedly exposed information includes usernames, email addresses, dates of birth, and hashed or plaintext passwords. The purported breach also reportedly includes technical identifiers such as IP addresses and browser user agent details. Most critically, the actor states that private messages between users and records of website activity are part of the leak. The claimed file size of 982 MB for the uncompressed data suggests the inclusion of extensive logs or message history, which could provide significant context about user interactions on the platform.
Threat Actor Profile
The poster, “0BITS,” does not appear to be a widely recognized or established threat actor based on the provided alias. The post is straightforward and lacks any grandstanding, ransom demands, or political motive, presenting the leak as a simple data dump for peer consumption. A significant red flag is the note that the post was edited by “Automation,” which is an atypical detail for a standard forum breach announcement and may indicate the use of automated posting scripts or a less sophisticated operation. The actor provides no history, reputation, or proof of previous breaches, making their credibility difficult to assess.
Potential Impact
If the claims are true, the impact on the alleged 1,186 affected users could be severe. The combination of email addresses, dates of birth, passwords, and private messages creates a high-risk scenario for identity theft, targeted phishing campaigns, and credential stuffing attacks. Given Iron March’s historical association with specific online communities, the exposure of private messages and activity logs could lead to reputational damage, harassment, or doxxing of individuals. The inclusion of IP addresses could also pose physical security risks by potentially revealing users’ approximate geographical locations.
What to Watch For
Security teams should monitor for the alleged MD5 hash (C77B413D5882201232EA6610BD8E4A4C) appearing in malware or breach databases. Individuals who may have had an account on the Iron March platform should be vigilant for targeted phishing emails referencing specific private messages or personal details allegedly contained in the dump. Researchers should look for any secondary posts or sales of this data on other dark web markets to corroborate the claim. The relatively low record count (1,186) is specific, but the lack of any data samples or credential previews in the public post is a notable omission that warrants skepticism.
Disclaimer
This report details an unverified claim from a dark web forum. Yazoul Security has not independently confirmed the breach of Iron March or the validity of the alleged data. The information presented is based solely on the threat actor’s post and should be treated as unsubstantiated. The presence of a file hash does not constitute proof that the data is genuine or that a breach occurred. This analysis is for proactive threat intelligence purposes only.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
Mag. Fünder Hausverwaltungs GmbH — incransom
Clearwater Marine Aquarium — qilin
Gruppo ICM SPA — qilin
Limkon — qilin