Panera Bread Database Allegedly Leaked - 14 Million Records Exposed
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
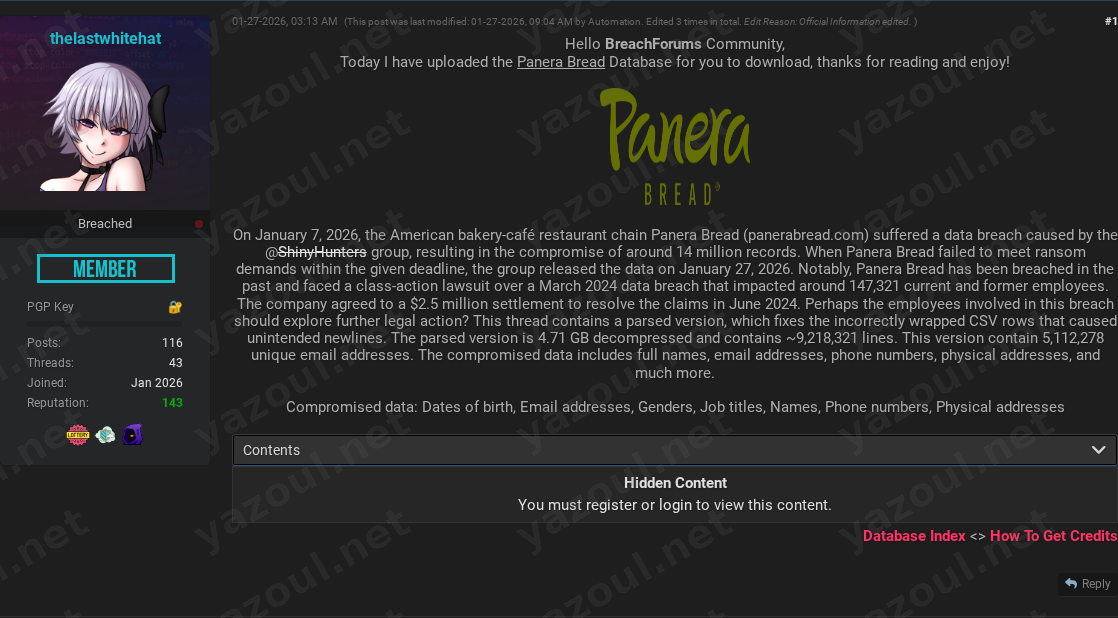
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
An unverified claim has surfaced on a dark web forum alleging a significant data breach at the American bakery-café chain Panera Bread. A user posting under the alias “thelastwhitehat” claims to have uploaded a database containing approximately 14 million records for download. According to the post, the data was purportedly stolen by the known threat group ShinyHunters following a failed ransom negotiation, with an alleged breach date of January 7, 2026, and a public release date of January 27, 2026. The poster provides technical details, including a file hash and data volume, and references the company’s history of prior breaches to lend credibility to the claim.
What Is Allegedly Exposed
The threat actor claims the compromised database contains a wide array of sensitive personal information. The alleged data types include full names, email addresses, phone numbers, and physical addresses. More sensitive details such as dates of birth, genders, and job titles are also purportedly included. The post states the parsed dataset contains over 9.2 million lines with more than 5.1 million unique email addresses, suggesting a mix of customer and potentially employee data. The actor claims the uncompressed file size is 4.72 GB and provides an MD5 hash (33D7264492CE6D833D9E5279DE384CB3) for verification.
Threat Actor Profile
The post is authored by “thelastwhitehat,” an alias with no established reputation or prior posting history visible in this context, which is a significant red flag. However, the claim attempts to borrow credibility by attributing the original breach to “ShinyHunters,” a well-known and prolific threat group with a history of high-profile attacks and data extortion. This association cannot be verified from the post alone. The detailed technical data (hash, record counts, file sizes) and the reference to Panera’s 2024 breach settlement are tactics commonly used to make a claim appear more legitimate.
Potential Impact
If the claim is valid, the potential impact is severe. The alleged exposure of dates of birth, physical addresses, and phone numbers in conjunction with names and emails creates a high risk for targeted phishing, identity theft, and financial fraud against millions of individuals. The inclusion of job titles could facilitate highly convincing spear-phishing campaigns against employees or corporate partners. Furthermore, the claim references Panera’s previous $2.5 million settlement for a 2024 breach, suggesting this alleged new incident could trigger significant legal, regulatory, and reputational consequences, eroding customer trust.
What to Watch For
- Official Confirmation: Monitor for any official statement or breach notification from Panera Bread regarding these allegations.
- Data Circulation: Watch for the alleged dataset or subsets appearing on other cybercriminal forums, ransomware leak sites, or credential-stuffing lists, which would substantiate the claim.
- ShinyHunters’ Communication: Although the post mentions the group, independent confirmation from ShinyHunters themselves via their typical channels would be a key indicator.
- Victim Reporting: An increase in targeted phishing attempts or fraud reports from individuals claiming to be Panera customers could be a downstream effect.
- Analyst Validation: Independent cybersecurity researchers or threat intelligence firms may attempt to validate the provided file hash or find samples of the data to assess the claim’s authenticity.
Disclaimer
This report details an unverified claim from a dark web forum. The information presented here is based solely on the threat actor’s post and has not been independently confirmed by Yazoul Security, Panera Bread, or any law enforcement agency. The alleged breach, its scale, the involvement of ShinyHunters, and the contents of the data are all speculative at this time. The provided details, including file hashes and record counts, should be treated as potentially fabricated or exaggerated. This report is for informational and situational awareness purposes only.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
Mag. Fünder Hausverwaltungs GmbH — incransom
Clearwater Marine Aquarium — qilin
Gruppo ICM SPA — qilin
Limkon — qilin