Ticketek User Database Allegedly Leaked - 30 Million Records Exposed
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
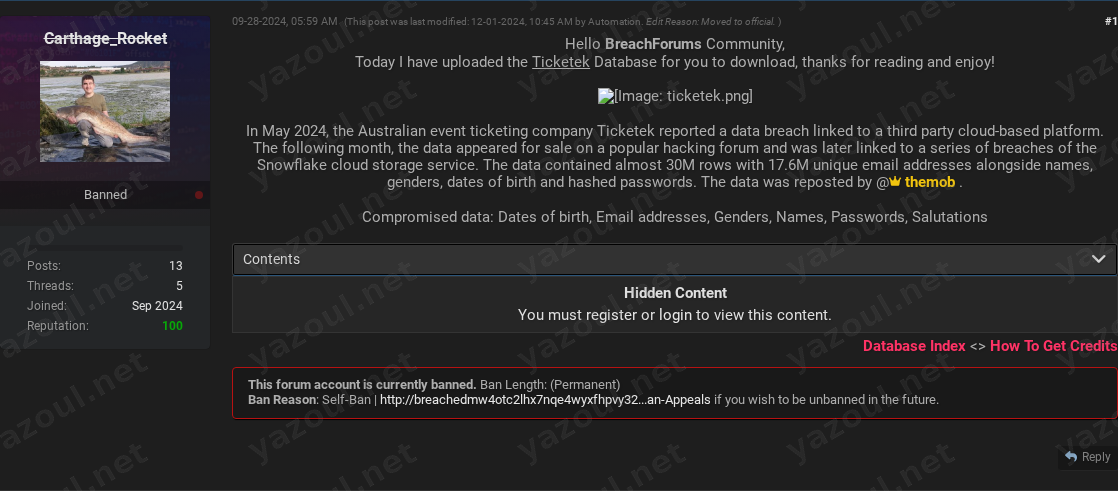
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
A threat actor using the alias “Carthage_Rocket” has posted on a dark web forum, claiming to have leaked a database allegedly belonging to the Australian ticketing company Ticketek. The post, dated September 28, 2024, and later edited in December, offers the purported data for download. The actor claims the dataset contains nearly 30 million records, including approximately 17.6 million unique email addresses. The post references a known breach incident from May 2024, linking this leak to data that was previously offered for sale and allegedly connected to breaches of the Snowflake cloud storage service. The post includes a file hash and size details, but no sample data is publicly visible.
What Is Allegedly Exposed
According to the unverified claims, the compromised data allegedly includes a wide range of personal information. The threat actor specifies that the dataset contains names, email addresses, genders, dates of birth, and salutations (like Mr., Ms.). Most critically, the post also claims that hashed passwords are included in the leak. The presence of hashed passwords, if true, could significantly increase the risk of credential-stuffing attacks if the hashing algorithm is weak or cracked. The actor states the uncompressed data file is approximately 6.87GB in size.
Threat Actor Profile
The post author, “Carthage_Rocket,” does not appear to be a widely recognized or established threat actor based on the provided information, which is a potential red flag for credibility. The post explicitly credits another entity, “@themob,” with reposting the data. “Themob” is a known alias associated with previous data breach sales and leaks. The involvement of this more established name could lend some superficial credibility to the claim, but it does not constitute verification. The post’s structure, including a detailed breach background and file hash, mimics legitimate leak posts, but the actor’s own reputation is unproven.
Potential Impact
If the claims are accurate, the potential impact is severe due to the sensitivity and volume of the data involved. The alleged inclusion of dates of birth and hashed passwords creates a high-risk scenario for identity theft and account takeover. Affected individuals could face targeted phishing campaigns, credential-stuffing attacks on other platforms where they reuse passwords, and financial fraud. For Ticketek, such a leak could lead to significant reputational damage, regulatory scrutiny under laws like Australia’s Privacy Act, and potential legal action from customers. The reference to the Snowflake incidents suggests this may be part of a broader, ongoing campaign affecting multiple organizations.
What to Watch For
Organizations and individuals should monitor for several key indicators. First, watch for the alleged data appearing on other cybercrime forums or clear web leak sites. Second, an increase in targeted phishing emails pretending to be from Ticketek or related event partners is a likely consequence. Third, security researchers may begin to analyze the provided MD5 hash (F449FD2E8DE0307463C9D204AC177073) to see if it matches any known, previously circulated datasets from the Ticketek or Snowflake incidents. Finally, any official communication from Ticketek updating their May 2024 breach notification would be crucial. The lack of public data samples in the post remains a significant gap in validating the claim.
Disclaimer
This report details unverified claims from a dark web forum. The information presented here is based solely on a single forum post and has not been independently confirmed by Yazoul Security, Ticketek, or any law enforcement agency. The scale of the alleged breach, the specific data types involved, and the very existence of this new leak remain unsubstantiated. All claims should be treated as alleged until verified by official sources. This report is for situational awareness and proactive threat intelligence purposes only.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
Mag. Fünder Hausverwaltungs GmbH — incransom
Clearwater Marine Aquarium — qilin
Gruppo ICM SPA — qilin
Limkon — qilin