Yellow Pages Directory Breach Claim — 28.5 million Records
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
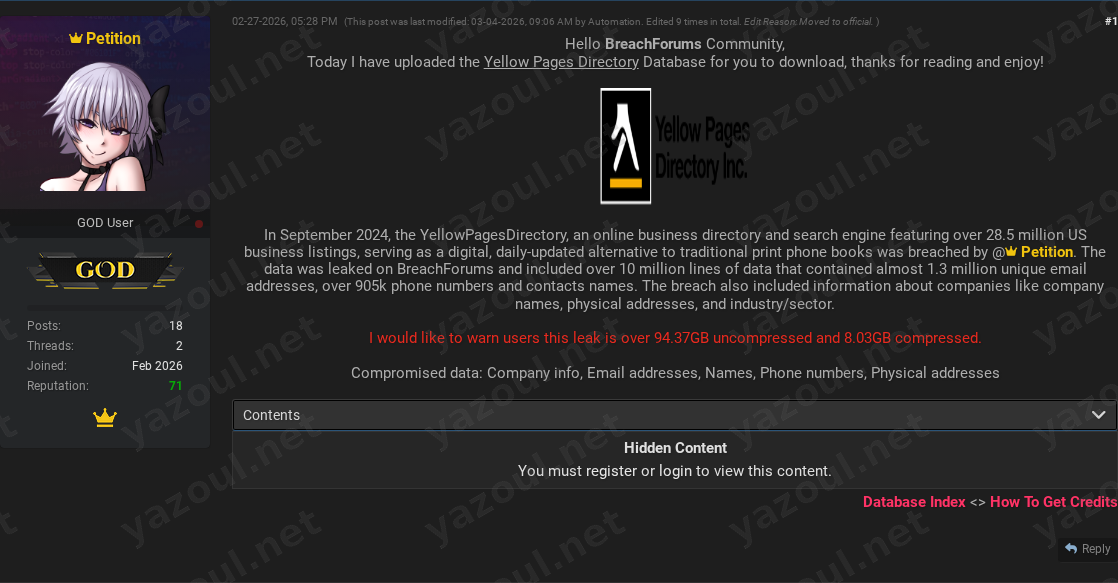
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
An unverified dark web forum post, dated February 27, 2026, alleges a significant data breach targeting Yellow Pages Directory. The post, authored by a user named “Petition,” claims to have leaked the entire business directory database. According to the post, the breach purportedly occurred in September 2024 and involves approximately 28.5 million records related to US business listings. The threat actor has made the data available for download on the forum, providing a file hash and details on the dataset’s size. The post has been edited multiple times, with a note indicating it was moved to an “official” section by an automated process, potentially suggesting some level of forum moderation or validation of the claim.
What Is Allegedly Exposed
The compromised data is claimed to be a comprehensive business directory. The alleged dataset reportedly includes company information such as names and physical addresses, along with contact details like individual names, email addresses, and phone numbers. The post specifies that the data contains millions of these data points, including a claimed 1.3 million unique email addresses and over 905,000 phone numbers. It is important to note that this constitutes business-to-business (B2B) and professional contact information, not consumer customer data. The threat actor provided an MD5 hash (EC6CA14FDFE4AD8FFA9D127F5DA60717) for the compressed file and noted the data is 94.37 GB when uncompressed.
Threat Actor Profile
The post is attributed to a user named “Petition.” The name is not widely recognized among established or high-reputation threat actors in recent intelligence reporting, which raises immediate questions about credibility. The post claims the breach was executed by this actor in 2024, but the posting date is 2026, indicating a potential delay in leaking the data or a recycled claim. The provided file hash adds a layer of technical specificity, allowing for potential verification if the file is encountered elsewhere. However, the lack of a known reputation for “Petition” and the absence of any data samples or proof-of-hack evidence in the public post are significant red flags.
Potential Impact
If the claims are true, the exposure of 28.5 million business records could have substantial repercussions. The alleged data types are prime targets for business email compromise (BEC) campaigns, highly targeted spear-phishing, and spam operations. Malicious actors could use the detailed company and contact information to impersonate businesses, craft convincing fraudulent invoices, or launch sophisticated social engineering attacks against employees. Furthermore, the aggregation of this data could facilitate large-scale profiling of the US business landscape. Organizations listed in the directory could face an increased risk of fraud and cyber-attacks targeting their personnel.
What to Watch For
- Verification of Data: Security researchers and threat intelligence platforms may attempt to validate the MD5 hash or find the dataset in other underground sources. Confirmation would likely come from independent analysis of the data’s contents.
- Yellow Pages Directory Response: Monitor for any official statement from Yellow Pages Directory regarding a potential breach. A lack of comment or a denial does not inherently validate or invalidate the claim.
- Actor Activity: Watch for follow-up posts by “Petition” or other actors claiming to sell or further distribute the data, which could indicate legitimacy.
- Downstream Use: An increase in targeted phishing campaigns or spam waves leveraging the specific business contact details described would be a strong indicator that the data is in active malicious use.
- Data Sample Appearances: Be cautious of any sites or actors offering “sample” records from this alleged breach as proof; these could be fabricated or sourced from older, public directories.
Disclaimer
This report details an unverified claim from a dark web forum. Yazoul Security has not independently confirmed the breach of Yellow Pages Directory, the validity of the leaked data, or the threat actor’s claims. The information presented is based solely on the forum post and should be treated as alleged and potentially fabricated. The existence of a file hash does not confirm the contents or origin of the data. Organizations should practice vigilance but avoid definitive conclusions until corroborating evidence emerges from credible sources.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
Mag. Fünder Hausverwaltungs GmbH — incransom
Clearwater Marine Aquarium — qilin
Gruppo ICM SPA — qilin
Limkon — qilin