0xy0um0m Databases: 6m Records Allegedly Leaked
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
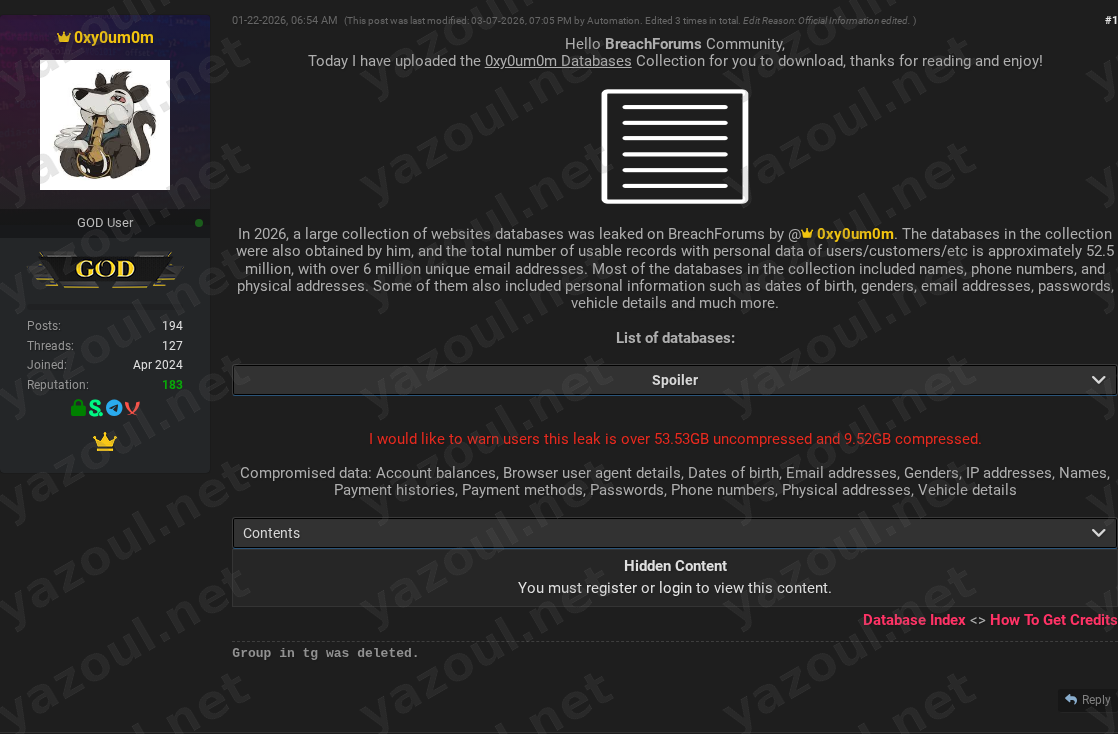
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
A threat actor using the alias “0xy0um0m” has posted on a dark web forum, allegedly leaking a massive collection of databases from various websites. According to the unverified post, the aggregated dataset contains approximately 52.5 million records with over 6 million unique email addresses. The actor claims the data was compiled from at least 17 different organizations, spanning e-commerce, services, and government entities across multiple countries. The post, which was reportedly edited multiple times by an automated process, offers the data for download, stating the compressed file is 9.52GB in size.
What Is Allegedly Exposed
The threat actor claims the aggregated collection contains a wide array of sensitive personal and financial data. The alleged data types include names, phone numbers, physical addresses, email addresses, dates of birth, genders, and passwords. More sensitive financial information is also purportedly present, including account balances, payment histories, and payment methods. Technical and device data such as IP addresses and browser user agent details are also listed, along with specific details like vehicle information. The post includes a list of purported source databases, naming specific domains and tables with individual record counts, such as a Thai service platform with over 17 million records and an Indian civic platform with over 25 million user records.
Threat Actor Profile
The post author, “0xy0um0m,” is the central figure in this claim. There is no immediately verifiable reputation or history associated with this alias on mainstream threat intelligence platforms, suggesting they may be a new or low-profile actor. The post’s structure, which includes formalized sections like “Contents” and “Database Index,” mimics the style of established leak sites or data brokers, potentially in an attempt to appear more credible. A significant red flag is the post’s metadata, indicating it was “Edited 3 times” by an entity named “Automation,” which is an unusual detail for a typical forum post and may suggest the content is managed or recycled.
Potential Impact
If the claims are true, the scale and sensitivity of the alleged data would represent a severe privacy and security incident. The combination of personal identifiers, financial data, and passwords across millions of individuals could facilitate widespread identity theft, financial fraud, and highly targeted phishing campaigns. The inclusion of data from what appears to be a government website (senado.leg.br) raises additional concerns about potential targeting of public officials or citizens engaged with governmental services. The aggregation of data from multiple sources also increases the risk of credential stuffing attacks, as users often reuse passwords across different services.
What to Watch For
Organizations named in the list of databases should be monitored for official breach notifications or statements. Security researchers may attempt to validate the file hash (602A35430B768FD929149902B05ED1AC) against known breach corpora. Watch for the alleged data appearing in other criminal marketplaces or being used in active phishing campaigns. Be skeptical of the actor’s claims regarding the total record count (52.5 million) and the specific inclusion of highly sensitive fields like account balances and payment histories without any provided proof of concept or sample data. The lack of a clear motive or pricing in the public post is also notable.
Disclaimer
This report details an unverified claim from a dark web forum. Yazoul Security has not independently confirmed the breach, the legitimacy of the data, or the threat actor’s claims. The details presented are allegations made by the poster. The listed organizations have not been confirmed as compromised at this time. The provided file hash and data counts should be treated as unsubstantiated claims. This information is provided for situational awareness and proactive defense planning only.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
Mag. Fünder Hausverwaltungs GmbH — incransom
Clearwater Marine Aquarium — qilin
Gruppo ICM SPA — qilin
Limkon — qilin