Kannarr Eye Care Ransomware Claim by INC Ransom (Apr 2026)
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
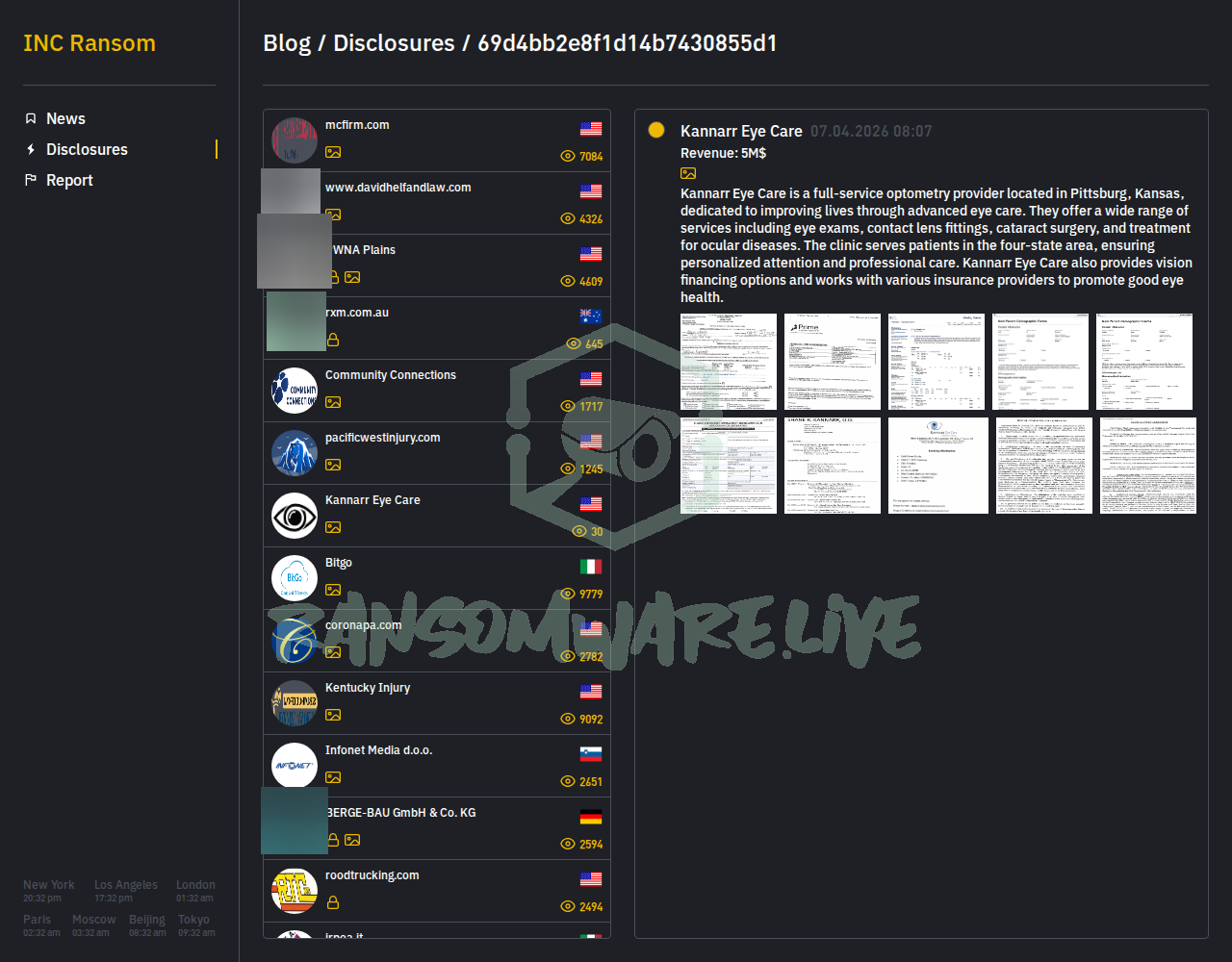
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
The ransomware group known as INC Ransom has posted an unverified claim of a cyberattack against Kannarr Eye Care, an optometry provider based in Pittsburg, Kansas. According to the group’s leak site, the alleged intrusion occurred on or around April 10, 2026. The threat actor claims to have exfiltrated data from the organization but has not disclosed the specific volume of data stolen. The posted description of the victim’s services appears to be copied from public sources, which is a common tactic to lend credibility to a claim.
Threat Actor Profile
INC Ransom is an established ransomware-as-a-service (RaaS) operation with a significant track record, having claimed over 725 victims to date. The group is known for a double-extortion model, stealing data before deploying encryption and threatening to publish it if a ransom is not paid. Their known toolset, as documented by security researchers, includes reconnaissance and credential access tools like Mimikatz and AdFind, network scanners such as Advanced IP Scanner and SoftPerfect NetScan, and legitimate cloud storage services like BackBlaze, MEGA, and Restic for data exfiltration. They have also been observed using the “Finger” command for network enumeration. Secureworks attributes their activity to a threat cluster tracked as GOLD IONIC. Detection guidance, including YARA rules, has been published by researchers at firms like Huntress in relation to their use of living-off-the-land binaries (LOLBins) in deployment chains.
Alleged Data Exposure
The threat actor has not provided a sample or a detailed list of the allegedly stolen data. Based solely on the claim, the potential data at risk could relate to a healthcare provider’s operations. This might include sensitive patient information, such as medical histories, appointment details, insurance data, and financial information related to vision financing, though this is speculative and unconfirmed. The lack of a data sample or specifics is notable and may be a pressure tactic.
Potential Impact
As an alleged attack on a healthcare provider, this claim carries significant potential implications. If valid, a breach could disrupt critical patient care services, including scheduling and treatment. The exposure of protected health information (PHI) would constitute a serious regulatory violation under HIPAA, potentially leading to substantial fines, legal liability, and loss of patient trust. Even as an unverified claim, it could cause reputational damage and operational uncertainty for the targeted organization.
What to Watch For
Monitor for any official statement from Kannarr Eye Care regarding a cybersecurity incident. Watch the INC Ransom leak site for potential updates, such as the posting of data samples or a countdown timer, which would indicate an escalation in pressure tactics. Security teams, particularly in the healthcare sector, should review detection rules for the tools and TTPs associated with INC Ransom and GOLD IONIC, focusing on network scanning activity, credential dumping attempts, and unusual outbound traffic to cloud storage platforms.
Disclaimer
This report is based on an unverified claim from a ransomware group’s data leak site. The information presented here has not been independently confirmed by Yazoul Security or external sources. The details, including the scope of any alleged data theft and the impact on the organization, are solely the claims of the threat actor. Ransomware groups frequently exaggerate or fabricate claims to coerce victims into paying ransoms. This report is for informational and threat intelligence purposes only.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
Mag. Fünder Hausverwaltungs GmbH — incransom
Clearwater Marine Aquarium — qilin
Gruppo ICM SPA — qilin
Limkon — qilin