Campbell University Ransomware Claim by INC Ransom (April 2026)
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
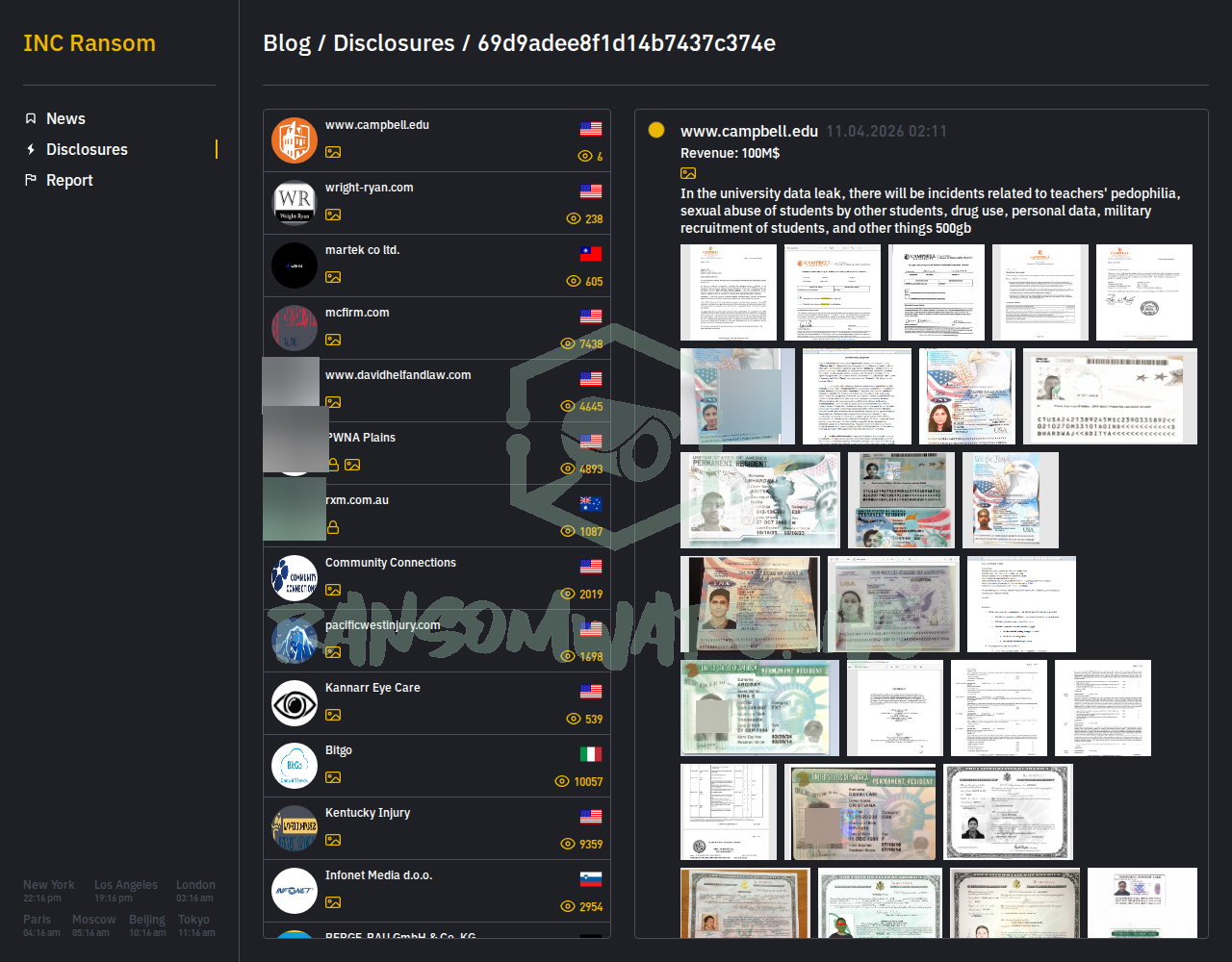
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
The ransomware group known as INC Ransom has listed Campbell University (www.campbell.edu) on its data leak site. The group claims to have executed an attack on April 11, 2026, and alleges to have exfiltrated approximately 500GB of data. The threat actor’s description of the data is highly sensational, claiming it contains information related to alleged teacher misconduct, student-on-student abuse, drug use, personal data, and military recruitment records. This claim has not been verified by independent sources.
Threat Actor Profile
INC Ransom is an established ransomware-as-a-service (RaaS) operation, linked to the initial access broker group “Gold Ionic” by Secureworks research. The group is known for a double-extortion model, stealing data before encryption. Their typical toolset, as observed in previous incidents, includes reconnaissance and credential harvesting tools like Mimikatz and AdFind, network scanners such as Advanced IP Scanner and SoftPerfect NetScan, and legitimate cloud storage services like BackBlaze, MEGA, and Restic for data exfiltration. The use of living-off-the-land binaries (LOLBins) is a noted tactic. Huntress has published analysis on their specific LOLBin use for deployment. The group has claimed over 725 victims, indicating significant operational activity, though the validity of each claim varies.
Alleged Data Exposure
According to the unverified post, the stolen 500GB dataset purportedly contains:
- Personal data of students and staff.
- Sensitive internal allegations and reports concerning misconduct.
- Information related to student military recruitment. The threat actor’s description employs inflammatory language, which is a common pressure tactic. The actual content, volume, and authenticity of the alleged data remain unconfirmed.
Potential Impact
If the claim is valid, the potential impact on Campbell University could be severe. The exposure of personal data could lead to identity theft and phishing campaigns targeting the university community. The release of sensitive, unverified allegations-regardless of their truth-could cause significant reputational damage, erode trust within the campus community, and potentially trigger legal and regulatory scrutiny. The education sector is a frequent target due to the vast amounts of personal data held and often decentralized IT security.
What to Watch For
- Official Statement: Monitor for an official incident notification or denial from Campbell University.
- Data Dump: INC Ransom typically sets a deadline before leaking data. Watch for any purported data samples appearing on other cybercriminal forums.
- IoC Propagation: Security researchers may publish indicators of compromise (IoCs) or YARA rules associated with this campaign if evidence emerges. The existing Huntress blog on INC Ransom’s techniques provides relevant detection guidance for the group’s known behaviors.
- Copycat Claims: Other actors may falsely associate themselves with the incident.
Disclaimer
This report is based on an unverified claim from a ransomware group’s data leak site. The allegations made by INC Ransom have not been independently confirmed by Yazoul Security, Campbell University, or any law enforcement agency. The details provided, including the nature of the data and the success of the attack, should be treated as potential disinformation or exaggeration intended to coerce the victim. This report is for defensive threat intelligence purposes only.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
Mag. Fünder Hausverwaltungs GmbH — incransom
Clearwater Marine Aquarium — qilin
Gruppo ICM SPA — qilin
Limkon — qilin