Mastercom Ransomware Claim by INC Ransom (Apr 2026)
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
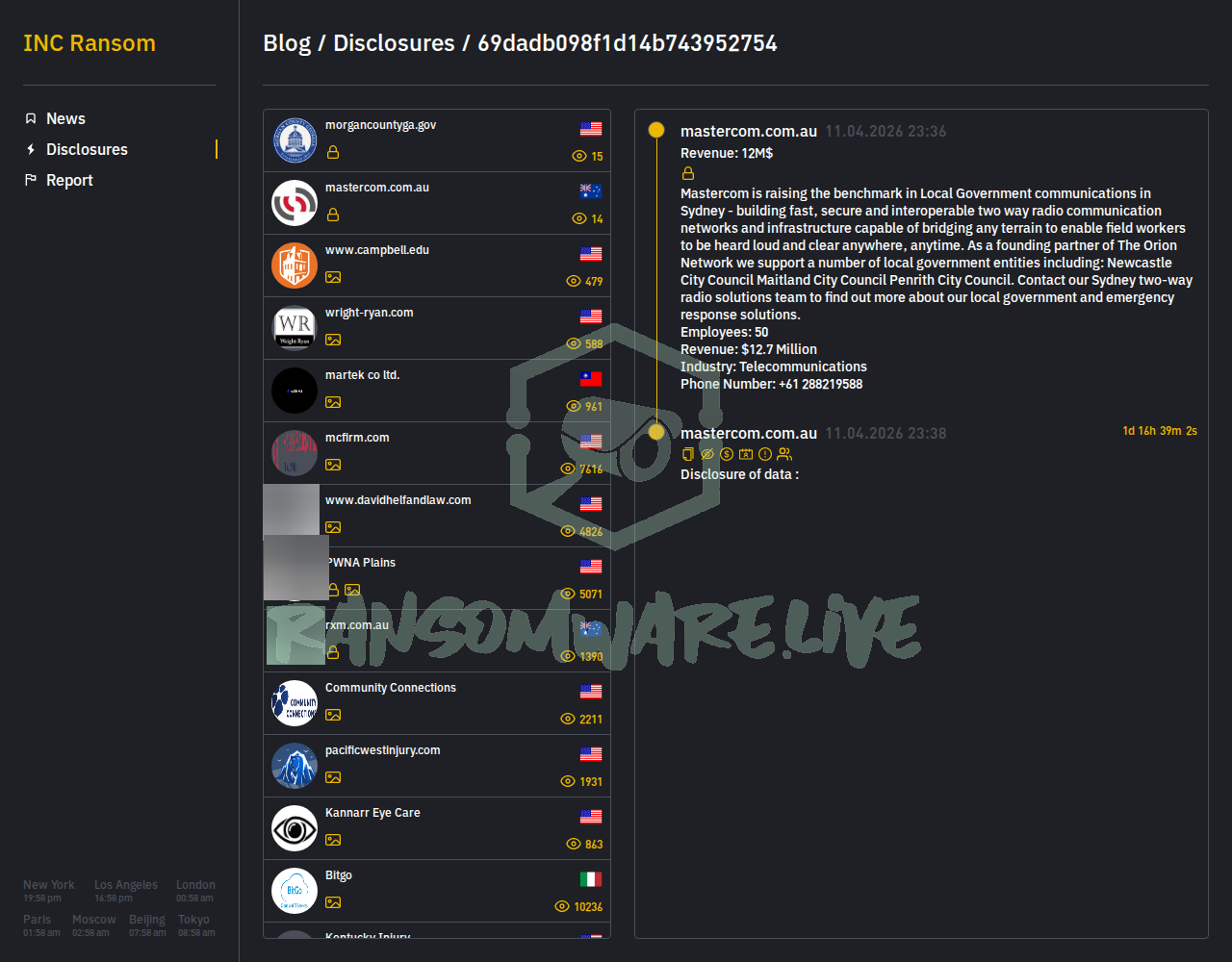
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
The ransomware group known as INC Ransom has listed the Australian telecommunications company Mastercom (mastercom.com.au) on its data leak site. The group claims to have executed an attack on April 11, 2026. The posted entry includes a description of Mastercom’s business, which focuses on building two-way radio networks for local government and emergency services in the Sydney area, naming Newcastle, Maitland, and Penrith City Councils as supported entities. The threat actor also lists corporate details such as employee count, revenue, and a phone number. The specific volume of data allegedly stolen has not been disclosed.
Threat Actor Profile
INC Ransom is an established ransomware-as-a-service (RaaS) operation with a significant track record, having claimed over 725 victims to date. The group is known for a double-extortion model, stealing data before encryption and threatening to publish it. Their known toolset includes credential access tools like Mimikatz, network discovery utilities such as AdFind, Advanced IP Scanner, and SoftPerfect NetScan, and exfiltration tools including BackBlaze, MEGA, and Restic. Research indicates they have used legitimate, signed binaries (LOLBins) in their attacks to evade detection. Secureworks attributes their activity to a threat cluster tracked as “Gold Ionic.”
Alleged Data Exposure
Based on the group’s post, the compromised data purportedly relates to Mastercom’s core business operations. The threat actor claims to have accessed information that could detail the company’s work with several local government councils and its emergency response solutions. While no specific data types (e.g., contracts, network diagrams, employee PII) are enumerated, the implication is that sensitive information regarding critical communications infrastructure and government partnerships may be at risk. The group has not provided samples or proof of the alleged data at this time.
Potential Impact
If the claim is valid, the potential impact is high given Mastercom’s role in supporting local government and emergency services communications. A breach could compromise sensitive information about critical radio network infrastructure, client contracts, and operational details. This could pose security risks to the named council entities, potentially affecting field worker communications and emergency response coordination. For Mastercom, the incident could lead to significant reputational damage, regulatory scrutiny, and operational disruption.
What to Watch For
Monitor for any further updates on INC Ransom’s leak site, including potential data dumps or proof-of-hack posts. Organizations, particularly in the telecommunications and local government sectors, should review detection guidance related to INC Ransom’s known tools. The Huntress blog referenced in intelligence mentions the use of a LOLBin (Finger) for command and control, which can inform defensive hunting. YARA rules or specific IOCs from the referenced Secureworks report may be available for network and endpoint detection.
Disclaimer
This report is based on an unverified claim from a ransomware group’s data leak site. The information presented here, including the details of the alleged attack and data exposure, has not been independently confirmed by Yazoul Security or external sources. Ransomware groups frequently exaggerate claims to pressure victims into paying ransoms. This analysis is for informational and threat intelligence purposes only.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
Mag. Fünder Hausverwaltungs GmbH — incransom
Clearwater Marine Aquarium — qilin
Gruppo ICM SPA — qilin
Limkon — qilin