Morgan County GA Ransomware Claim by INC Ransom (April 2026)
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
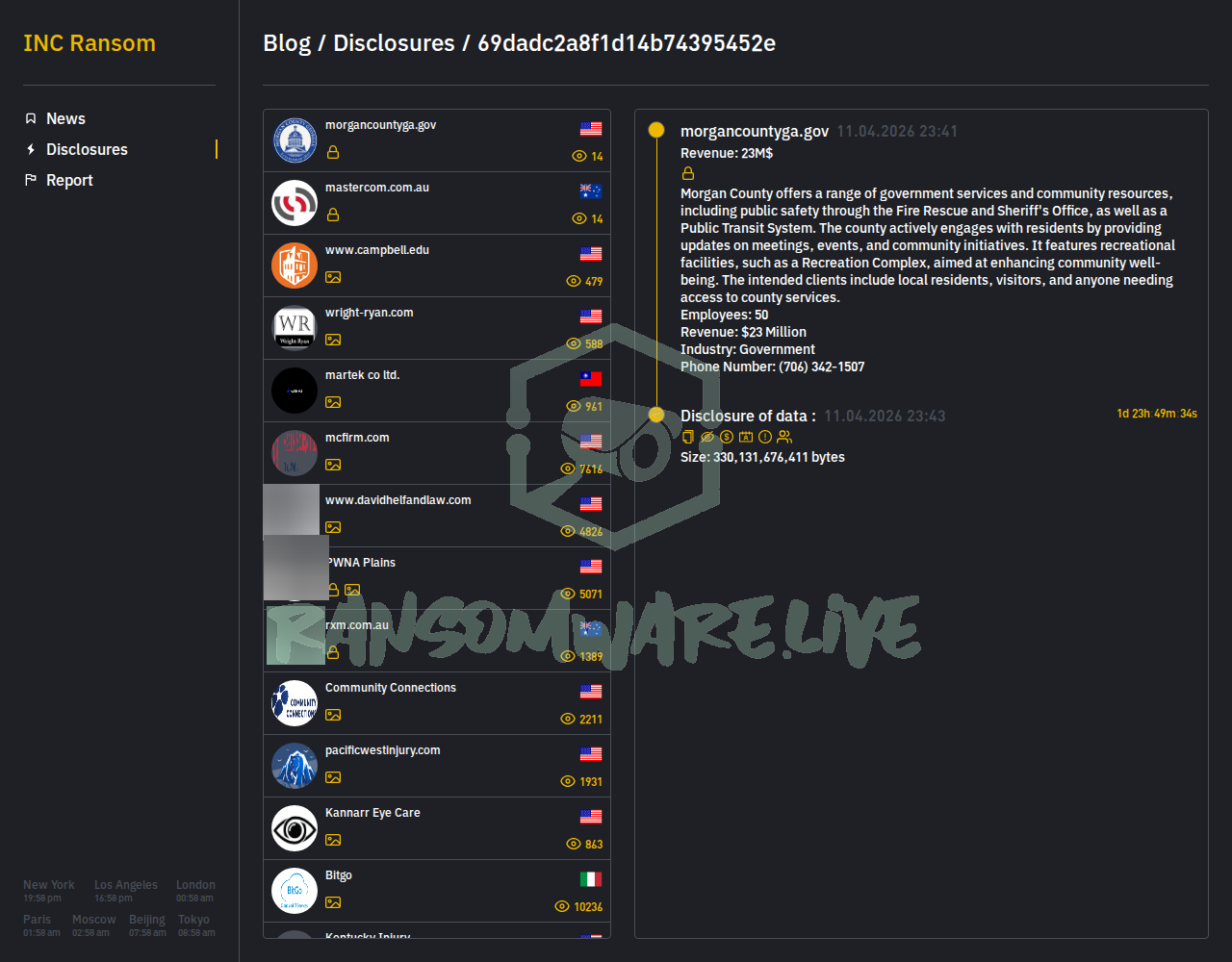
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
The ransomware group known as INC Ransom has posted an unverified claim of a cyberattack against Morgan County, Georgia (morgancountyga.gov). According to their leak site, the alleged intrusion occurred on April 11, 2026. The threat actor’s post describes the county’s operations, highlighting public safety services like the Sheriff’s Office and Fire Rescue, public transit, and recreational facilities. The group claims to have accessed data but has not disclosed the specific volume or types of files exfiltrated at this time. The listed employee count is 50 with a revenue of $23 million.
Threat Actor Profile
INC Ransom is an established ransomware-as-a-service (RaaS) operation with a significant track record, having claimed over 725 victims. The group is known for a double-extortion model, stealing data before encryption and threatening to publish it. Their known toolset includes credential access tools like Mimikatz, network discovery utilities such as AdFind and Advanced IP Scanner, and exfiltration tools including BackBlaze, MEGA, and Restic. Secureworks research associates the group with a threat cluster dubbed “Gold Ionic,” noting their use of living-off-the-land binaries (LOLBins) for deployment. Huntress has also documented their TTPs, including the use of the finger command for reconnaissance. Security firms have published detection guidance, including YARA rules, based on their custom ransomware binary and deployment scripts.
Alleged Data Exposure
While INC Ransom has not provided a detailed data leak or samples in this initial claim, the descriptive nature of their post suggests they purportedly gained access to systems managing sensitive county functions. The implied scope includes information related to public safety operations (Sheriff’s Office, Fire Rescue), public transit, community initiatives, and resident services. The potential exposure could involve internal administrative data, resident information, or operational details. The group typically follows up with proof packs, so the absence of specific file lists is not unusual for an initial posting.
Potential Impact
As a local government entity, Morgan County manages critical public safety and resident services. A confirmed breach could disrupt emergency response coordination, transit services, and public communications. The exposure of resident data could lead to privacy violations and identity theft risks. Furthermore, such an attack could erode public trust in local government’s ability to protect sensitive information. Operational downtime from system encryption could delay essential services like permitting, court functions, and utility management.
What to Watch For
- Proof of Claims: Monitor for follow-up posts from INC Ransom that may include file tree listings, document samples, or screenshots as proof of the alleged breach.
- Official Statement: Await an official incident notification or statement from Morgan County government authorities.
- Broader Campaigns: Given INC Ransom’s high volume of attacks, this may be part of a broader targeting campaign against municipal or county governments.
- IOCs and Detection: Security teams should review existing YARA rules and detection logic for INC Ransom tools and binaries, paying close attention to network scanning activity and the use of cloud storage services for data exfiltration.
Disclaimer
This report is based on an unverified claim from a ransomware group’s data leak site. The information presented here, including the alleged attack, data exposure, and group details, has NOT been independently confirmed by Yazoul Security or external sources. Ransomware groups frequently exaggerate claims to pressure victims into paying. This analysis is for defensive threat intelligence purposes only. Organizations should not treat this as a confirmed breach without official verification from the affected entity.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
Mag. Fünder Hausverwaltungs GmbH — incransom
Clearwater Marine Aquarium — qilin
Gruppo ICM SPA — qilin
Limkon — qilin