Gastroenterology & Hepatology of CNY Hit by Exitium (Apr 2026)
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
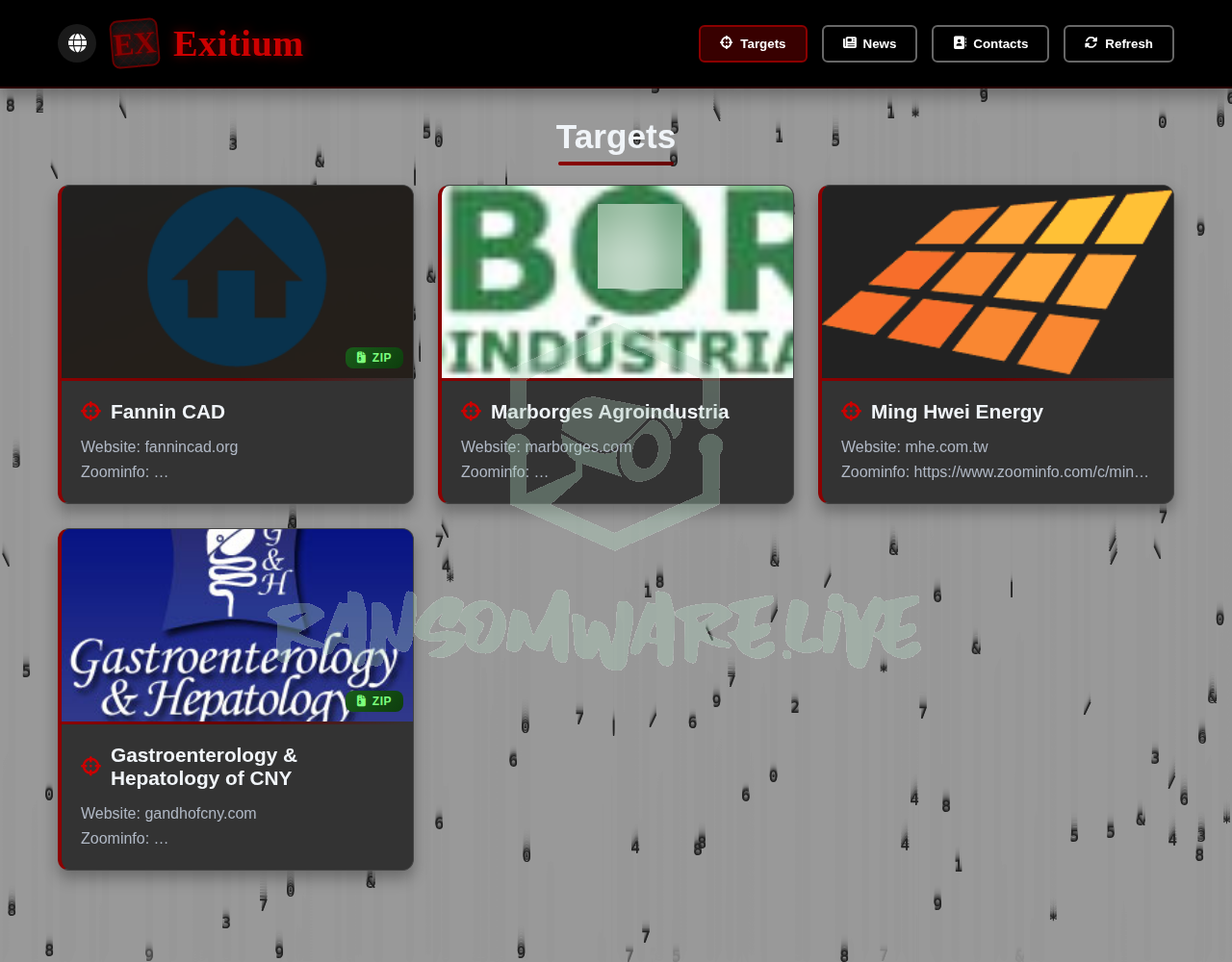
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
The ransomware group known as Exitium has posted an unverified claim of an attack against Gastroenterology & Hepatology of CNY, P.C., a healthcare provider and AAAHC-accredited endoscopy center based in Syracuse, New York. The group alleges the attack occurred on April 14, 2026. According to the threat actor’s post, data was allegedly exfiltrated from the organization’s primary website domain and a related entity, the Digestive Disease Center of CNY, LLC. Exitium claims it is selling the “full database” and has provided a detailed breakdown of the allegedly stolen records. The group states the entire internal dataset will be sold if a ransom is not paid.
Threat Actor Profile
Exitium is a relatively new or low-profile ransomware operation with minimal public footprint. Based on available intelligence, this group has only one publicly claimed victim at this time, suggesting it may be an emerging threat or a rebrand of another entity. There is no publicly available research, known tools, tactics, or procedures (TTPs), or YARA rules specifically attributed to the Exitium group. This lack of historical data makes it difficult to assess their technical capabilities or typical attack vectors. Their credibility and the authenticity of their claims remain unverified.
Alleged Data Exposure
The threat actor claims to possess a comprehensive database of patient records. The alleged data includes:
- Patient Records: 167,303 total patient records, with 124,761 allegedly containing Social Security Numbers (SSNs). The claim states 166,402 records include addresses, 164,296 include phone numbers, and 85,318 include email addresses.
- Medical Data: 1,093,863 diagnoses (ICD-10 codes), 1,547,142 medication records, and 186,246 pathology specimens with narrative reports.
- Sensitive Health Information: The group specifically highlights data on 49,798 patients with sensitive diagnoses and medications, including claims of records related to mental health (43,902), substance/alcohol use (5,111), sexually transmitted infections (2,779), cancer (2,708), and Hepatitis C (1,906).
- Notable Individuals: The post alleges the data includes information on politicians, businesspeople, and other public figures.
Potential Impact
If verified, this alleged breach would constitute a significant healthcare data compromise. The exposure of SSNs combined with highly sensitive medical diagnoses creates severe risks for affected individuals, including identity theft, targeted phishing, medical fraud, and personal extortion. For the healthcare provider, such an incident could result in substantial regulatory penalties under HIPAA, loss of patient trust, legal liabilities, and operational disruption. The claim that data includes notable individuals could attract additional media and law enforcement scrutiny.
What to Watch For
- Verification: Monitor for any official statement from Gastroenterology & Hepatology of CNY or its affiliated entities regarding a cybersecurity incident.
- Data Dump: Watch for any actual leakage of the claimed data on cybercrime forums or leak sites, which would substantiate the threat actor’s claims.
- Exitium Activity: Observe if Exitium claims further victims or provides more details about their methods, which could help in profiling the group.
- Regulatory Filings: Potential HIPAA breach notifications to the U.S. Department of Health and Human Services and affected individuals, if the incident is confirmed.
Disclaimer
This report is based on an unverified claim from a ransomware group’s data leak site. The information presented here has NOT been independently confirmed by Yazoul Security or external sources. Ransomware groups frequently exaggerate the scope and sensitivity of stolen data to coerce victims into paying ransoms. The details regarding data volume, content, and the attack itself should be treated as allegations until corroborated by reliable evidence or an official statement from the affected organization.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
Mag. Fünder Hausverwaltungs GmbH — incransom
Clearwater Marine Aquarium — qilin
Gruppo ICM SPA — qilin
Limkon — qilin