Rhode-HV Ransomware Attack by Krybit (April 2026)
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
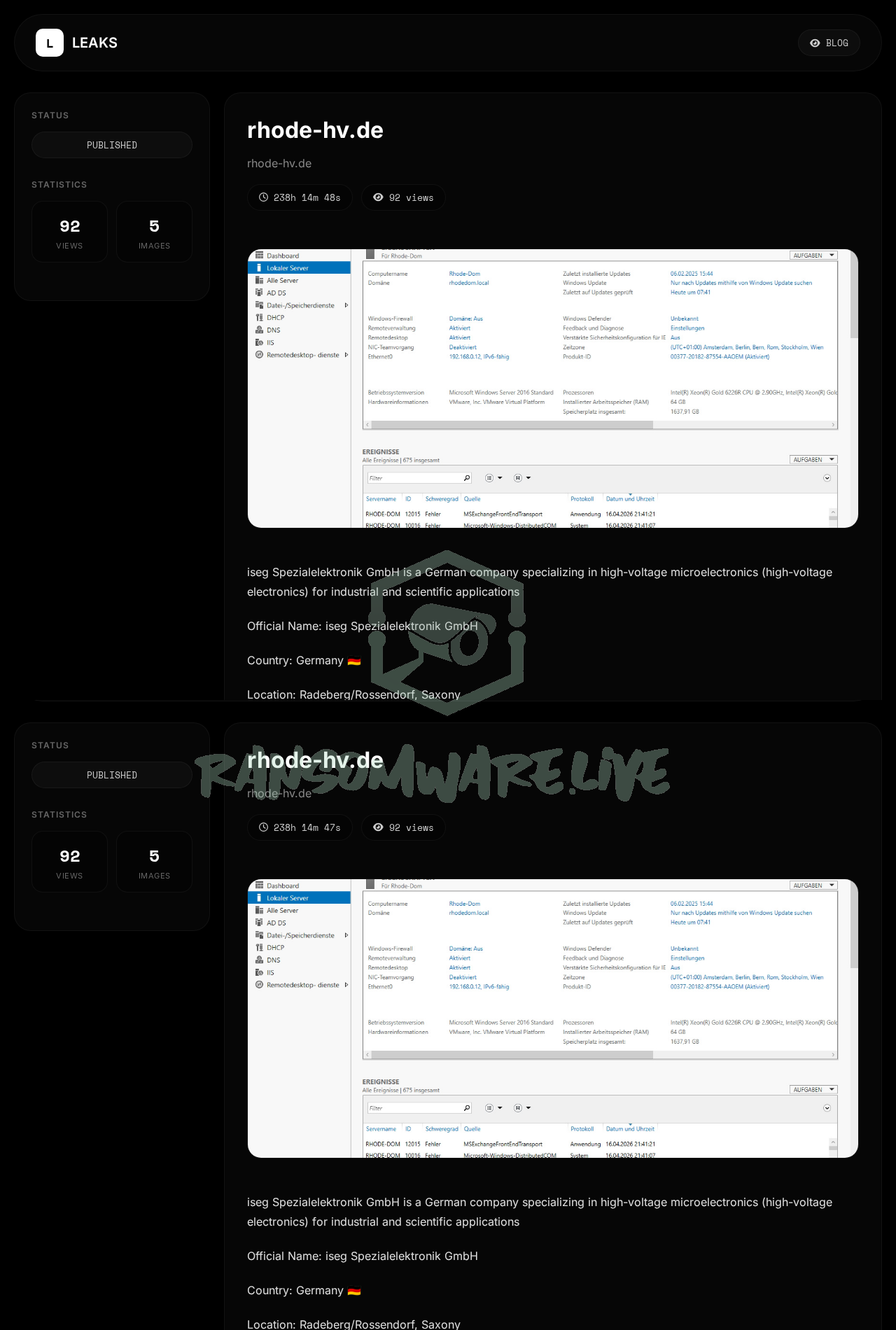
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
The ransomware group known as Krybit has posted an entry on its data leak site, allegedly claiming responsibility for a cyberattack against the German manufacturing organization Rhode-HV, operating under the domain rhode-hv.de. According to the threat actor’s post, the intrusion occurred on April 17, 2026. The group claims to have exfiltrated data related to “iseg Spezialelektronik GmbH,” which is described as a company specializing in high-voltage microelectronics. The exact volume of the allegedly stolen data has not been disclosed by the threat actor.
Threat Actor Profile
Krybit is a relatively low-profile ransomware operation with limited public visibility. There is no significant public research or reliable intelligence reporting on this group’s tactics, techniques, and procedures (TTPs). Its total number of known victims is unclear, and its preferred tools, infrastructure, or ransom models are not documented in open-source threat intelligence communities. The lack of a known track record makes it difficult to assess the group’s operational sophistication or the credibility of its claims. They may be a new group, a rebrand of another operation, or a less active player attempting to gain notoriety.
Alleged Data Exposure
The threat actor purports to have stolen data associated with high-voltage electronics. While specific file types or databases are not listed, the mention of “iseg Spezialelektronik GmbH” suggests the targeted information could include proprietary technical data, product specifications, manufacturing processes, or potentially sensitive commercial documents. Without independent verification, the nature, scope, and authenticity of this alleged data breach remain entirely unconfirmed.
Potential Impact
If the claim is valid, a breach of a specialized manufacturing firm like Rhode-HV could have several implications. The theft of intellectual property related to high-voltage electronics could undermine competitive advantage, lead to significant financial loss, and potentially compromise product safety if sensitive design data is manipulated or leaked. For the organization, this could result in operational disruption, regulatory scrutiny-especially under frameworks like the EU’s NIS2 Directive-and reputational damage within a niche industrial sector. However, given the unverified nature of the claim, these impacts are purely speculative.
What to Watch For
- Official Statement: Monitor for any official confirmation or denial from Rhode-HV or its affiliated entities regarding a security incident.
- Data Appearance: Watch for any of the allegedly stolen data appearing on other cybercriminal forums, paste sites, or through data breach monitoring services.
- Group Activity: Observe if Krybit posts additional victims or provides “proof” packs (samples of the stolen data) to bolster their claim, which could indicate a more active and credible campaign.
- Sector Targeting: Note if other German manufacturing or high-tech industrial firms report similar incidents, which could suggest a broader targeting campaign rather than an isolated attack.
Disclaimer
This report is based on an unverified claim from a ransomware group’s data leak site. The information presented here has NOT been independently confirmed by Yazoul Security or external sources. The alleged victim organization has not been verified as compromised. Ransomware groups frequently exaggerate or fabricate claims to extort payments and gain publicity. This intelligence should be treated as unconfirmed and used for situational awareness and proactive defense planning only.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
Marino Food Products Pvt — payload
Franziskusschule Wilhelmshaven — payload
orientalweavers.com — payload
Sunlight Express Airways — payload