GRUPO RONDA Ransomware Claim by Lamashtu (April 2026)
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
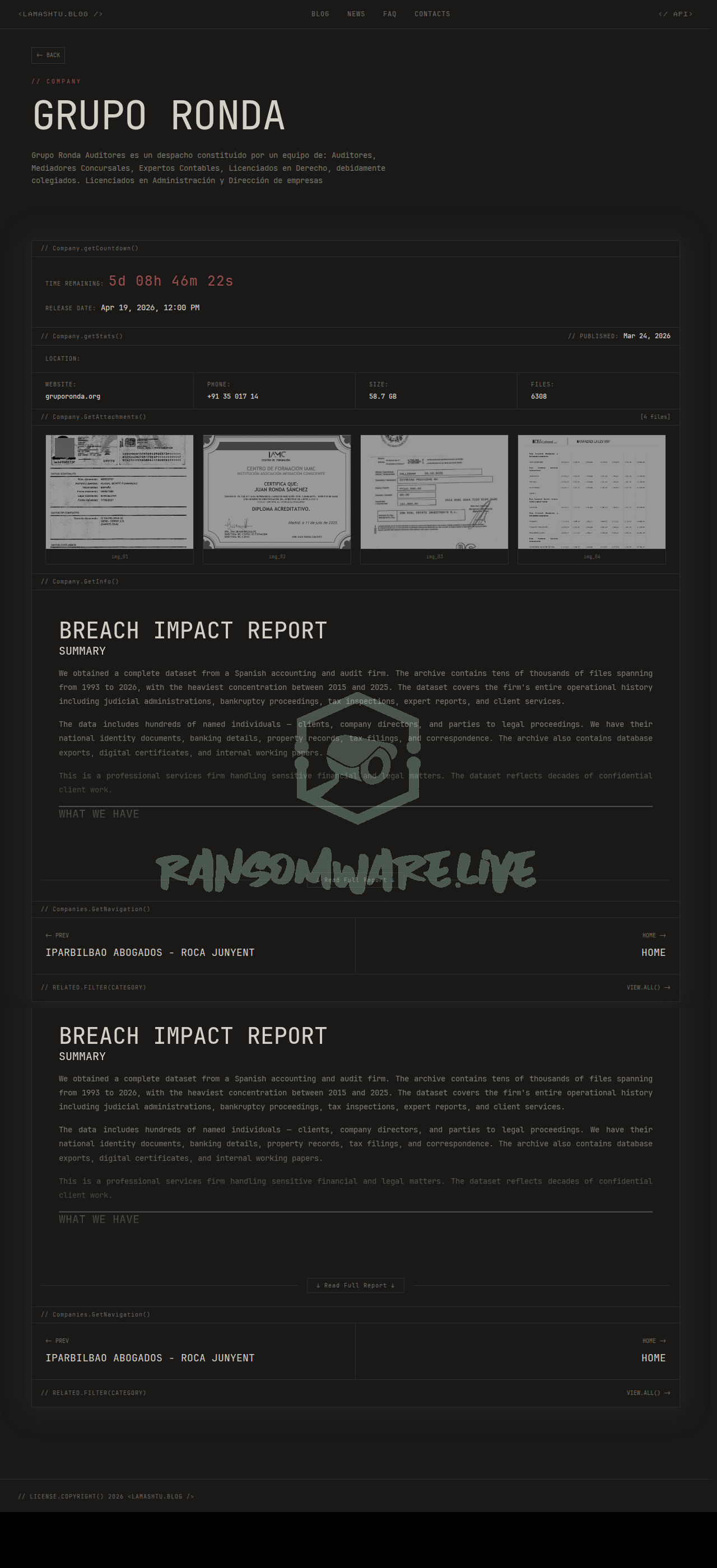
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
The Lamashtu ransomware group has posted an unverified claim of a cyberattack against GRUPO RONDA, a business services firm based in Mexico. According to the group’s leak site, the alleged intrusion occurred on April 14, 2026. The threat actor claims to have compromised data from the organization, which operates under the domain gruporonda.org. The posted description suggests the victim firm is a professional services office comprised of auditors, insolvency mediators, accounting experts, and licensed legal and business administration professionals. The exact volume of data allegedly stolen has not been disclosed by the group.
Threat Actor Profile
The Lamashtu ransomware operation has a limited public footprint, with no significant research references or detailed analyses widely available. Key characteristics such as its total number of known victims, preferred initial access vectors, and known tools or malware families remain undisclosed or unconfirmed by cybersecurity researchers. This lack of a verifiable track record makes it difficult to assess the group’s technical sophistication or the credibility of its claims. Groups with low visibility sometimes exaggerate claims to gain notoriety or pressure victims into paying ransoms. No specific YARA rules or detection guidance for Lamashtu infrastructure or tools are publicly referenced at this time.
Alleged Data Exposure
Based on the description provided by Lamashtu, the compromised data purportedly relates to the firm’s core professional services. This could include sensitive information pertaining to audit processes, financial records, legal case details, insolvency mediation documents, and confidential client data handled by licensed professionals. The claim suggests exposure of information that is highly confidential and protected by professional privilege laws in many jurisdictions. However, the group has not provided any samples or proof of the data to substantiate these allegations.
Potential Impact
If the claim is valid, the potential impact on GRUPO RONDA and its clients is severe. A breach of audit and legal data could lead to significant financial, legal, and reputational damage. Clients may face risks of fraud, identity theft, or exposure of sensitive business dealings. For the firm itself, such an incident could trigger regulatory scrutiny under Mexican data protection laws, lead to loss of client trust, and result in substantial recovery and remediation costs. The professional nature of the services makes the alleged data particularly sensitive.
What to Watch For
Monitor for any further communications from the Lamashtu group, such as the release of proof-of-hack data or an increased ransom deadline. Watch for potential data dumps on other cybercriminal forums. Organizations in the business services and professional advisory sector, particularly in Latin America, should review their security posture, as emerging or low-profile groups may target similar firms. There is no specific IOCs or TTPs associated with Lamashtu publicly available, so general ransomware defense best practices are advised.
Disclaimer
This report is based on an unverified claim from a ransomware group’s data leak site. Yazoul Security has NOT independently confirmed the breach of GRUPO RONDA. The details, including the scope of data allegedly stolen and the group’s capabilities, are solely based on the threat actor’s statements. Ransomware groups frequently exaggerate claims to coerce victims into paying. This information is provided for situational awareness and defensive intelligence purposes only.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
rhode-hv.de — krybit
Marino Food Products Pvt — payload
Franziskusschule Wilhelmshaven — payload
orientalweavers.com — payload