BBA Law Group Ransomware Claim by Safepay (April 2026)
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
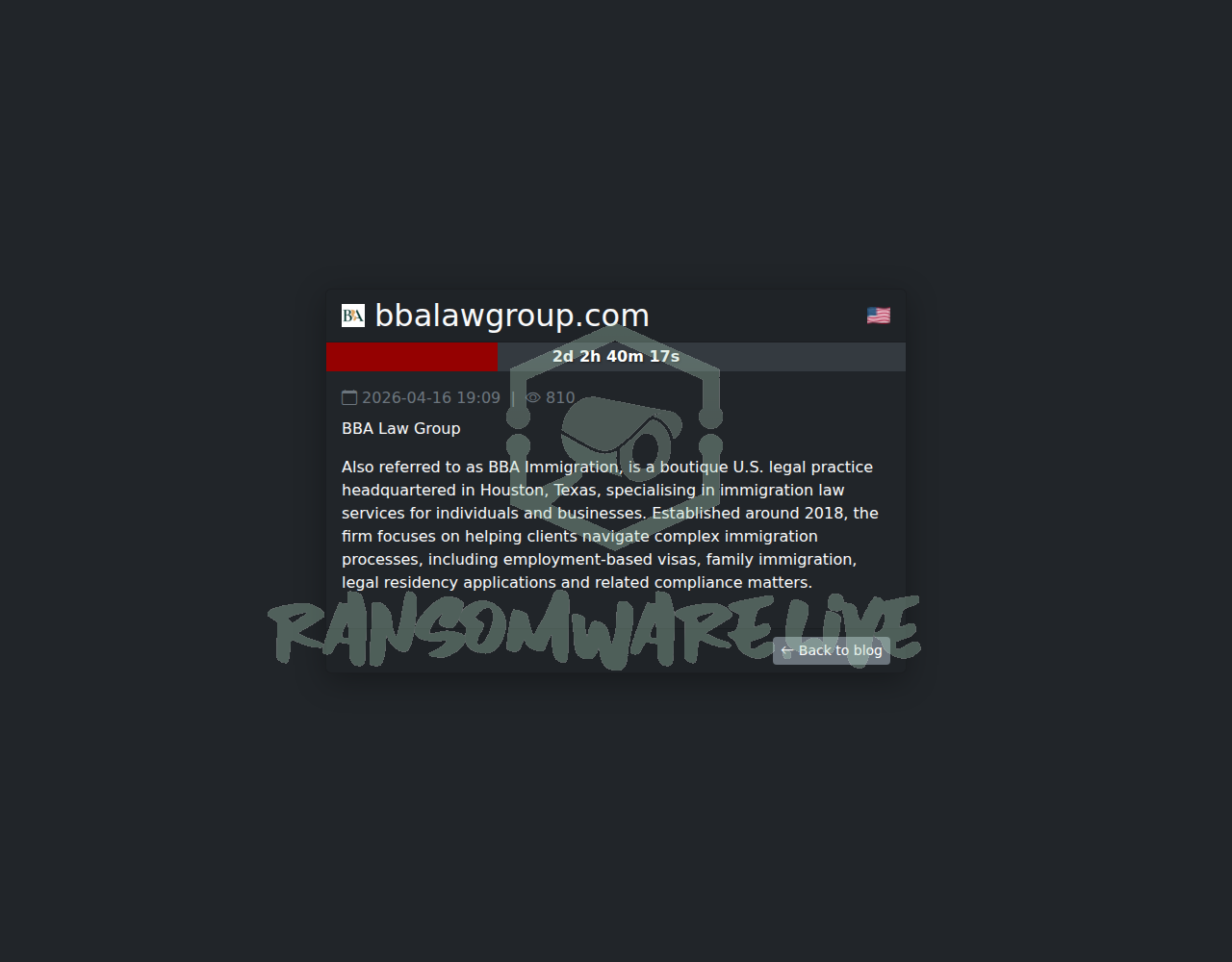
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
The Safepay ransomware group has posted an unverified claim of a cyberattack against BBA Law Group (bbalawgroup.com), a boutique immigration law practice based in Houston, Texas. According to the group’s leak site, the alleged intrusion occurred on April 17, 2026. The threat actor claims to have exfiltrated data from the firm but has not disclosed the specific volume of data stolen. The post references the firm’s specialization in U.S. immigration law, suggesting the targeted data may be highly sensitive.
Threat Actor Profile
Safepay is a ransomware-as-a-service (RaaS) operation with a significant volume of claimed attacks, listing 444 victims on its leak site at the time of this report. The group’s known toolset, as observed in previous incidents, includes common utilities for discovery and data staging, such as Invoke-ShareFinder for network reconnaissance, and archiving tools like 7-Zip and WinRAR for compressing stolen data prior to exfiltration. Their tactics also involve leveraging trusted system processes for execution, specifically CMSTPLUA, dllhost.exe, and Regsvr32.exe, which are often used in living-off-the-land (LotL) techniques to evade detection. There is no significant public threat intelligence research or YARA rules specifically attributed to Safepay campaigns, indicating they may operate with moderate sophistication while relying on established methods.
Alleged Data Exposure
The threat actor alleges the theft of data from BBA Law Group. Given the firm’s focus on immigration law, the compromised information could purportedly include highly confidential client data such as visa applications, passport details, financial records, case notes, and internal corporate documents. The exact nature and scope of the allegedly exfiltrated data remain undisclosed by the group, which is a common tactic to increase pressure on the victim during negotiations.
Potential Impact
If this claim is valid, the potential impact is severe due to the sensitive nature of immigration legal services. A data breach could lead to significant privacy violations for clients, exposing them to identity theft or fraud. For BBA Law Group, this could result in substantial legal liability, loss of client trust, regulatory penalties under laws like HIPAA (if medical data is involved) or state data breach statutes, and severe reputational damage. The firm’s operations could also be disrupted if systems were encrypted in the attack.
What to Watch For
Monitor for any official confirmation or denial from BBA Law Group regarding a security incident. Watch the threat actor’s leak site for potential data dumps, which they may use to escalate pressure. Security teams should review detection logs for the use of the mentioned tools (Invoke-ShareFinder, 7-Zip, WinRAR) and suspicious activity by processes like CMSTPLUA, dllhost.exe, and Regsvr32.exe, especially in conjunction with network share enumeration or large data transfers. Given the lack of public research, sharing anonymized IOCs with industry information sharing groups is advised.
Disclaimer
This report is based on an unverified claim from a ransomware group’s data leak site. Yazoul Security has not independently confirmed the breach of BBA Law Group. The details provided, including the attack date, tools used, and data allegedly stolen, are solely the claims of the Safepay threat actors. Ransomware groups frequently exaggerate or fabricate claims to extort payments. This information is provided for situational awareness and defensive cybersecurity purposes only.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
cheeky.com.ar — safepay
firstcambodia.com.kh — safepay
The Epoch Times — coinbasecartel
Flash Charm INC - (IDERA) — coinbasecartel