First Cambodia Ransomware Claim by Safepay (April 2026)
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
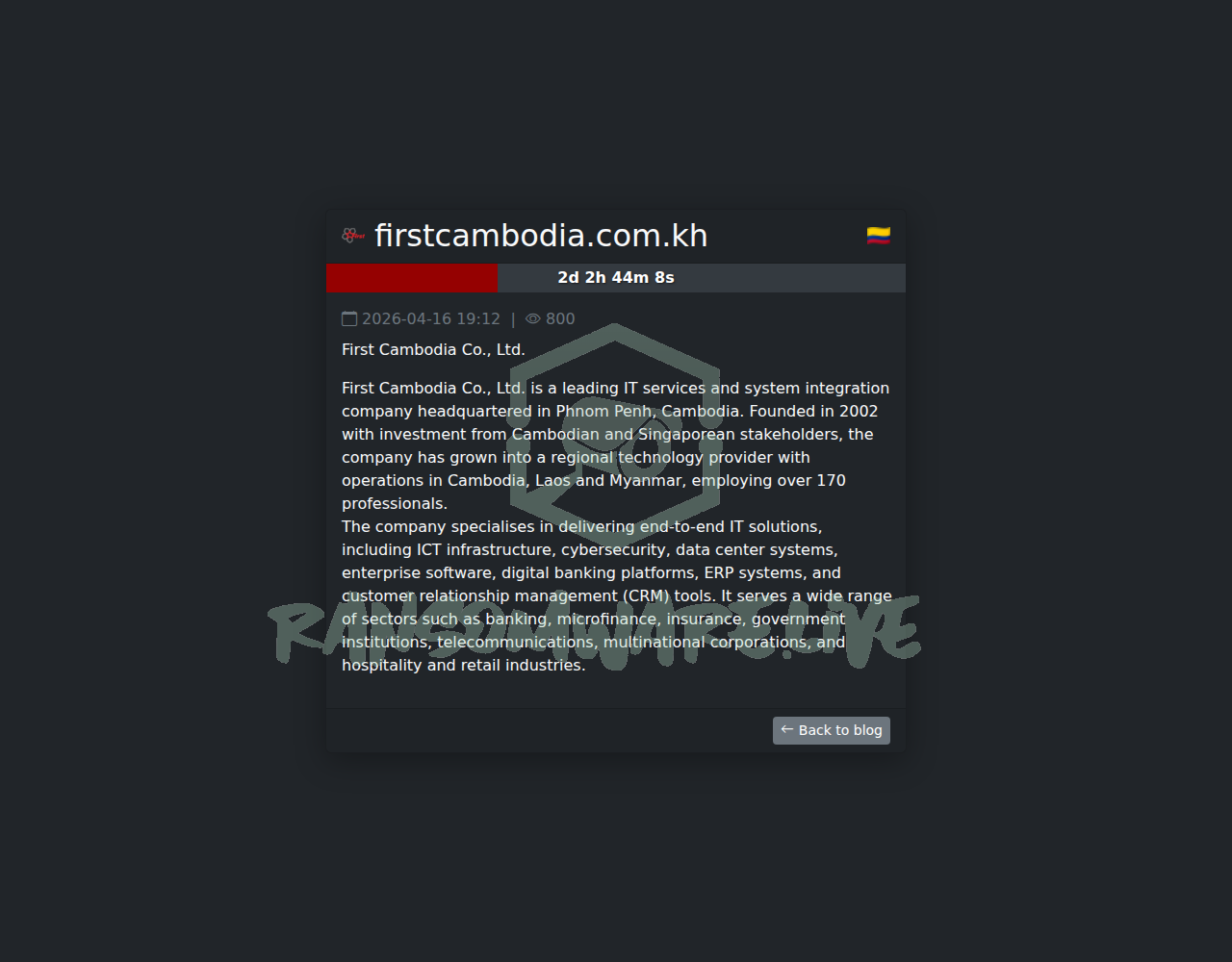
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
The Safepay ransomware group has listed the domain firstcambodia.com.kh, belonging to First Cambodia Co., Ltd., on its data leak site. The group claims to have executed an attack on April 17, 2026. According to the post, the victim is described as a leading IT services and system integration company based in Phnom Penh. The threat actor has not disclosed the volume of data allegedly stolen but has published what appears to be a company description, suggesting they may have accessed corporate documents. The authenticity of this claim has not been verified.
Threat Actor Profile
Safepay is a ransomware-as-a-service (RaaS) operation with a significant volume of activity, claiming over 440 victims to date. The group’s known toolset, as observed in previous incidents, includes living-off-the-land binaries (LOLBins) and common utilities to facilitate intrusion, data discovery, and exfiltration. Specifically, Safepay affiliates have reportedly used:
- Invoke-ShareFinder: A PowerShell script for network share discovery.
- Archiving Tools (7-Zip, WinRAR): Used to compress and prepare stolen data for exfiltration.
- LOLBins (CMSTPLUA, dllhost.exe, Regsvr32.exe): Legitimate Windows processes abused to execute malicious code and bypass application allowlisting.
This pattern indicates a focus on stealth and leveraging trusted system processes. No specific YARA rules or public detection guidance are widely documented for Safepay at this time, highlighting the need for robust monitoring of the listed tools and associated behaviors.
Alleged Data Exposure
The leak site entry does not provide a detailed data inventory or samples for public download. The primary content is a textual description of First Cambodia’s business, which the threat actor presumably extracted from internal documents or the company’s website. Based on this, the alleged compromise could involve corporate files, client information, project data, or internal communications. However, without evidence from the threat actor, the exact nature and sensitivity of the purportedly stolen data remain unclear.
Potential Impact
If the claim is valid, the impact on First Cambodia could be severe. As an IT services and system integration provider, a breach could compromise not only its own proprietary information and employee data but also potentially sensitive data related to its clients’ systems and infrastructure. This could lead to significant reputational damage, loss of client trust, regulatory scrutiny, and potential downstream attacks on its customer base. The hospitality and tourism sector in its region, which may rely on its services, could also be indirectly affected.
What to Watch For
- Data Dump: Monitor for Safepay following through on its threat by releasing actual data samples or a larger data archive.
- Secondary Claims: Watch for corroborating posts on other cybercriminal forums or claims from affiliated actors.
- Client Targeting: Organizations, particularly in the hospitality sector, that are clients of First Cambodia should be vigilant for any increase in phishing or credential-stuffing attempts using potentially leaked data.
- TTP Evolution: Security teams should incorporate the known Safepay tools (like Invoke-ShareFinder and abuse of CMSTPLUA) into their threat-hunting and detection strategies.
Disclaimer
This report is based on an unverified claim from a ransomware group’s data leak site. Yazoul Security has not independently confirmed the alleged breach of First Cambodia Co., Ltd. The details presented, including the attack date, tools used, and data involved, are solely the assertions of the Safepay threat actors. Ransomware groups frequently exaggerate claims to pressure victims into paying ransoms. This information is provided for situational awareness and defensive cybersecurity purposes only.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
bbalawgroup.com — safepay
cheeky.com.ar — safepay
The Epoch Times — coinbasecartel
Flash Charm INC - (IDERA) — coinbasecartel