Odido Database Allegedly Leaked - 6M Records Exposed
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
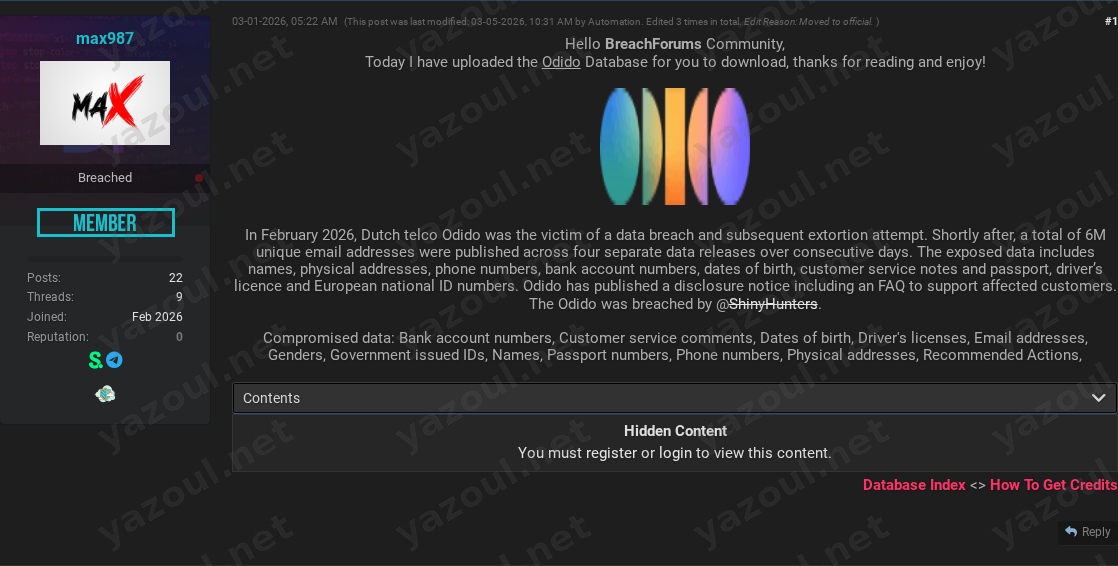
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
An unverified post on a dark web forum, authored by a user named “max987,” alleges the leak of a database belonging to the Dutch telecommunications company Odido. The post, dated March 1, 2026, claims to offer a download of this data, purportedly containing approximately 6 million records. The post references the well-known threat actor group ShinyHunters as the alleged perpetrators of the original breach, which is said to have occurred in February 2026. The post includes a file hash and details about the data’s compressed and uncompressed size.
What Is Allegedly Exposed
According to the post, the compromised dataset is extensive and highly sensitive. The alleged data types include:
- Personally Identifiable Information (PII): Full names, physical addresses, phone numbers, email addresses, dates of birth, and genders.
- Government-Issued Identification: Passport numbers, driver’s license numbers, and other government-issued ID numbers.
- Financial Data: Bank account numbers.
- Operational Data: Customer service comments and notes labeled as “Recommended Actions.”
The post claims the data is from customers of Odido, a major telecom provider in the Netherlands, which would significantly increase the sensitivity and potential impact of the leak if verified.
Threat Actor Profile
The post directly names the prolific threat group ShinyHunters as the entity responsible for the breach. ShinyHunters has a well-documented history of high-profile attacks and data extortion, lending a degree of contextual credibility to the claim. However, the actual forum poster, “max987,” is an unknown entity. The post appears to be a redistribution of previously leaked data rather than a new claim from the original actors. The inclusion of a specific MD5 hash (4E6DEB090C145FB3286A786F84E1DFF0) and file size details adds a layer of technical specificity often seen in credible leaks.
Potential Impact
If this alleged data is authentic, the impact on affected individuals could be severe. The combination of financial information (bank accounts) with high-value identity documents (passports, national IDs) and extensive PII creates a potent risk of:
- Identity Theft and Fraud: Enabling criminals to impersonate victims for financial gain or to establish fraudulent lines of credit.
- Targeted Phishing and Social Engineering: Armed with detailed personal and service history, attackers could craft highly convincing spear-phishing campaigns.
- Financial Fraud: Direct attempts to access or manipulate bank accounts.
- Reputational Damage: For Odido, handling a breach of this alleged scale would involve significant regulatory scrutiny, potential fines under laws like the GDPR, and loss of customer trust.
What to Watch For
- Corroboration: Monitor for official statements from Odido regarding this specific claim. Also, watch for other threat actors or sources discussing or validating the dataset’s authenticity.
- Data Activation: Look for signs of the alleged data being weaponized, such as targeted phishing campaigns referencing Odido or an increase in fraud attempts against individuals in the Netherlands.
- Actor Motivation: The post’s purpose seems to be redistribution. The credibility of the claim hinges more on the alleged original actor (ShinyHunters) than the poster. Be skeptical of any follow-up extortion attempts tied to this post.
- Regulatory Action: Potential investigations by Dutch data protection authorities could serve as indirect validation of a significant incident.
Disclaimer
This report is based on an unverified claim from a dark web forum. None of the information presented has been independently confirmed by Yazoul Security or external sources. The existence of the breach, the scope of the data, and the involvement of any specific threat actor are all allegations at this time. The details provided, including file hashes and data types, are taken solely from the forum post and should be treated as unsubstantiated claims until verified by official channels or credible evidence.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
bbalawgroup.com — safepay
cheeky.com.ar — safepay
firstcambodia.com.kh — safepay
The Epoch Times — coinbasecartel