BMW Hong Kong: 13978 records Records Allegedly Leaked
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
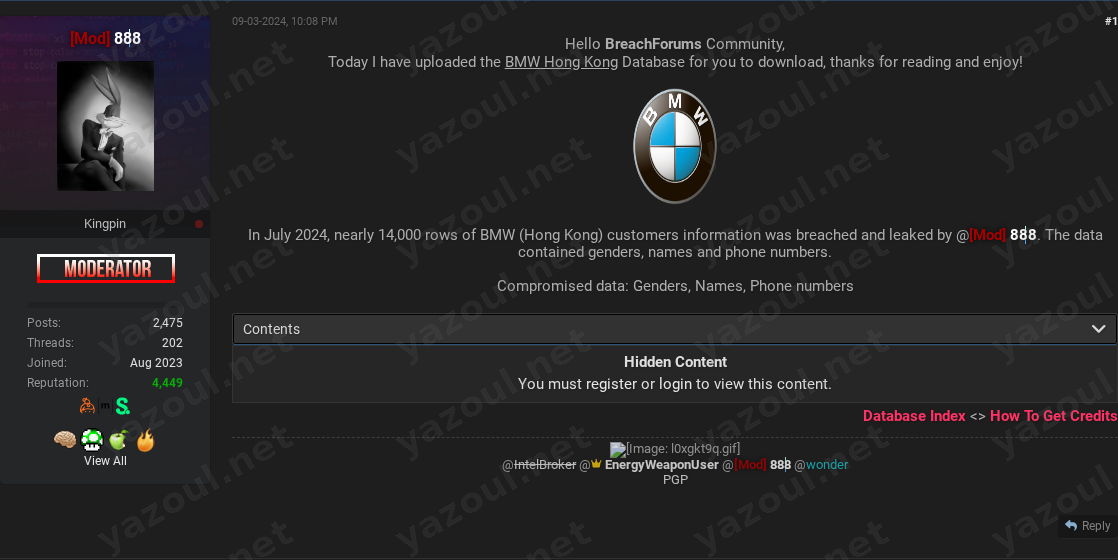
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
An actor using the alias “888” has posted an alleged data breach of BMW Hong Kong on a dark web forum. According to the unverified post, dated September 3, 2024, the actor claims to have leaked a database containing customer information. The post states the breach occurred in July 2024 and offers a compressed file for download, which purportedly contains nearly 14,000 records of personal data.
What Is Allegedly Exposed
The threat actor claims the compromised database includes 13,978 records of BMW Hong Kong customers. The data types allegedly exposed are limited to three fields: customer genders, full names, and phone numbers. The post provides technical details, including an MD5 file hash and file sizes (approximately 130KB compressed, 542KB uncompressed), which suggests the dataset is relatively small and contains only basic contact information. No financial data, addresses, or vehicle information is mentioned in the claim.
Threat Actor Profile
The post author is identified solely by the alias “888.” There is no readily available reputation or history associated with this alias on major threat intelligence platforms, suggesting this may be a new or low-profile actor. The lack of an established persona is a significant red flag for credibility. The actor provides no motive for the breach, such as extortion or hacktivism, and the post is presented as a simple data dump for the forum community.
Potential Impact
If the claim is valid, the exposure of names and phone numbers could facilitate targeted phishing campaigns (smishing) or vishing (voice phishing) attacks against BMW Hong Kong customers. Attackers could use the data to craft convincing, personalized messages pretending to be from BMW regarding vehicle services, recalls, or promotions. While the data types are not as sensitive as financial details or passwords, this information could be used for harassment, doxxing, or sold as a lead list to other spammers. The reputational impact on BMW Hong Kong, regardless of the claim’s veracity, could involve customer concern and require investigative and communication resources.
What to Watch For
- Verification of Data: Security researchers will likely attempt to validate the provided MD5 hash against known breaches or analyze any samples that may surface. Corroboration from other sources or victims is needed.
- Actor Activity: Monitor if “888” posts further claims or provides proof-of-hack evidence to bolster credibility.
- Data Usage: Watch for signs of the alleged data being utilized in phishing kits or spam campaigns targeting Hong Kong residents.
- Official Response: An official statement from BMW Group or BMW Hong Kong regarding an investigation would be a key indicator.
- Forum Credibility: The post’s reception within its forum community-whether it is downloaded, discussed, or dismissed-can offer informal credibility assessment.
Disclaimer
This report details an unverified claim from a dark web forum. Yazoul Security has not independently confirmed the breach of BMW Hong Kong or the validity of the alleged data. The information presented is based solely on the threat actor’s post and should be treated as unsubstantiated allegation. The presence of technical details like a file hash does not constitute proof of a genuine breach. Organizations should avoid using any provided hashes or links to search for or download the purported data, as this may pose a security risk.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
bbalawgroup.com — safepay
cheeky.com.ar — safepay
firstcambodia.com.kh — safepay
The Epoch Times — coinbasecartel