Cal AI: 3 million Records Allegedly Leaked
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
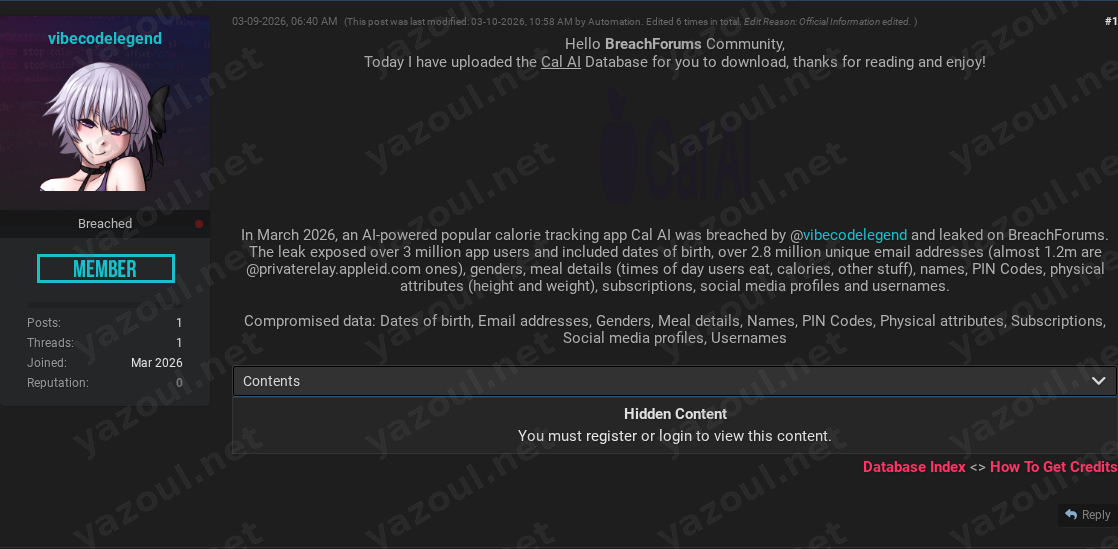
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
An unverified claim has surfaced on a dark web forum alleging a significant data breach of Cal AI, a purported AI-powered calorie tracking application. The post, authored by a user named “vibecodelegend,” claims to have leaked the company’s entire user database. According to the post, the leak occurred in March 2026 and allegedly exposes over 3 million user records. The threat actor has provided a file hash and specific data volume details, but no verifiable proof of the data’s authenticity has been made public. The post was heavily edited by an automated forum tool, which may indicate adherence to a specific posting template.
What Is Allegedly Exposed
The threat actor claims the leaked database contains a highly sensitive combination of personal, health, and authentication data. Allegedly exposed information includes user names, dates of birth, email addresses, genders, and usernames. More concerningly, the post states the data includes PIN codes, physical attributes like height and weight, meal details with timestamps and calorie information, subscription statuses, and linked social media profiles. A notable claim within the post is that nearly 1.2 million of the over 2.8 million unique email addresses are Apple privacy relay addresses, which, if true, could indicate a large iOS user base. The data is claimed to be extensive, with an uncompressed size of 14.25GB containing over 3 million records.
Threat Actor Profile
The post is attributed to “vibecodelegend,” an actor with no established reputation or prior notable claims on the forum. The account appears to be relatively new or low-profile, which is a significant red flag for credibility. The act of claiming responsibility for the breach (“breached by @vibecodelegend”) is common for actors seeking notoriety. The detailed, templated nature of the post and its multiple automated edits suggest the actor may be following a common forum format for data leak announcements, which does not inherently validate the claim. The lack of a known history makes it difficult to assess the actor’s typical tactics or the legitimacy of past claims.
Potential Impact
If the claims are true, the potential impact on affected users is severe. The combination of standard PII (names, DOB, emails) with highly sensitive health data (weight, height, meal habits) and authentication elements (PIN codes) creates a multifaceted risk. This data could be used for targeted phishing campaigns, identity theft, financial fraud, and extortion. The inclusion of meal details and physical attributes could also enable highly personalized social engineering or targeted advertising for dubious health products. For the organization, Cal AI, a confirmed breach of this nature would represent a catastrophic failure of data security, likely triggering regulatory scrutiny, legal action, and massive reputational damage, especially given the app’s health-focused purpose.
What to Watch For
Organizations and individuals should monitor for several key indicators. First, watch for any official statement from Cal AI regarding a potential security incident. Second, monitor other cybersecurity intelligence sources and data breach notification services for corroboration of this claim. Third, be alert for phishing campaigns that may leverage the specific types of data mentioned (e.g., emails referencing meal tracking or subscription details). Security researchers may attempt to validate the provided MD5 hash (AF3B0DCCE42FF7E4FFB966A0E73F53CB) against other known datasets, but the hash alone is not proof of content. The claim regarding Apple privacy relay addresses is a specific detail that, if observed in other contexts, could lend slight credibility to the overall allegation.
Disclaimer
This report details an unverified claim from a dark web forum. Yazoul Security has not independently confirmed the breach of Cal AI, the authenticity of the alleged data, or the number of records involved. The details presented are based solely on the threat actor’s post and should be treated as alleged and unsubstantiated. The presence of specific details like file hashes and data counts does not constitute proof of a genuine breach. This information is provided for situational awareness and proactive threat intelligence purposes only.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
bbalawgroup.com — safepay
cheeky.com.ar — safepay
firstcambodia.com.kh — safepay
The Epoch Times — coinbasecartel