Chronopost Pickup: 861k Records Allegedly Leaked
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
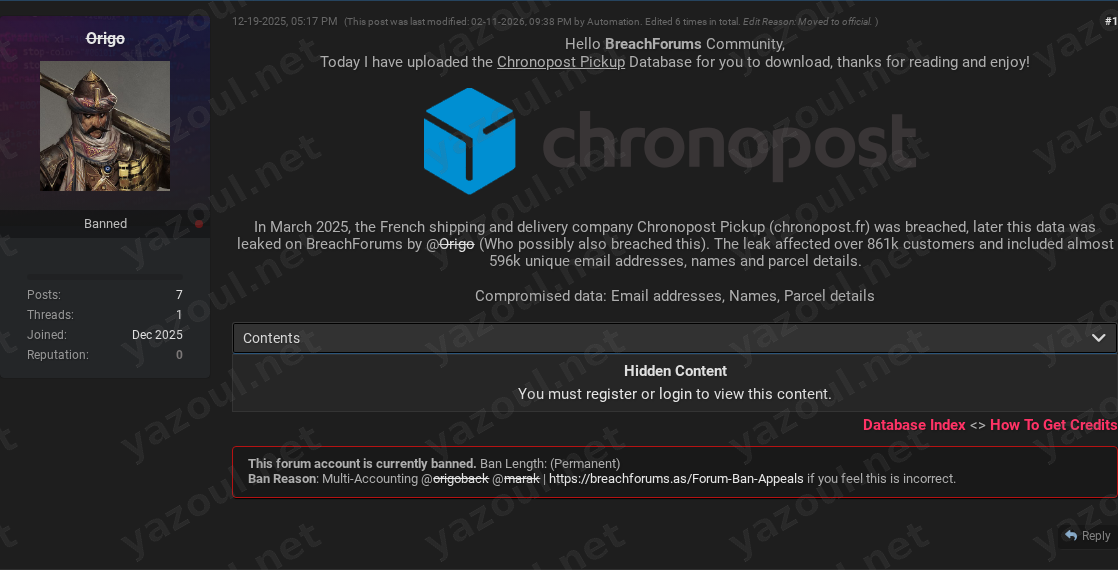
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
An unverified claim on a dark web forum alleges a significant data breach at Chronopost Pickup, a French shipping and delivery service. A user known as “Origo” posted a thread titled “Chronopost Pickup Database - Leaked, Download!” on December 19, 2025. The post claims to offer a database containing information on over 861,000 customers, purportedly compromised in March 2025. The post includes a file hash and size details, but the data itself has not been independently verified by Yazoul Security.
What Is Allegedly Exposed
According to the threat actor’s post, the compromised database allegedly contains approximately 861,084 records. The data types claimed to be exposed include:
- Personal Identifiers: Customer names and email addresses. The post specifies nearly 596,000 unique email addresses are included.
- Operational Data: Specific details related to parcels. The exact nature of these details (e.g., tracking numbers, delivery addresses, dates) is not specified in the public claim, but such data could potentially reveal customer shipping patterns and transactions.
The post provides an MD5 hash (4B7C34A04A37FF8741F6EEF02D8B6C77) for the alleged data file and notes its compressed and uncompressed sizes, which adds a layer of technical specificity to the claim.
Threat Actor Profile
The claim is made by a single actor using the pseudonym “Origo.” The post suggests this actor may have been responsible for the initial breach, but this is not confirmed. There is no widely recognized reputation or history associated with this alias in public threat intelligence reporting at this time, which is a significant red flag. The post was edited multiple times by an automated forum process and was later moved to an “official” section, which may imply some level of validation by forum moderators, though this does not equate to verification of the data’s authenticity.
Potential Impact
If the claim is valid, the alleged exposure poses several risks:
- Phishing and Spam Campaigns: The large cache of email addresses and associated names could be leveraged for targeted phishing emails, impersonating Chronopost to steal further credentials or financial information.
- Targeted Social Engineering: Combined parcel details could allow for highly convincing scams, where threat actors reference specific shipments to build trust with victims.
- Privacy Violations: The exposure of personal data linked to shipping activity could infringe on customer privacy and potentially be used for profiling.
- Reputational Damage: For Chronopost Pickup, such a breach could erode customer trust and necessitate costly incident response and regulatory compliance actions, particularly under laws like the GDPR.
What to Watch For
- Official Confirmation: Monitor for any public statement or data breach notification from Chronopost or its parent company.
- Data Circulation: Watch for the alleged dataset or subsets of it appearing on other cybercriminal platforms or in credential-stuffing attacks.
- Phishing Lures: Be alert for an increase in phishing emails impersonating Chronopost, especially those that reference specific shipping details.
- Actor Activity: Note if the “Origo” alias becomes associated with other data leaks, which could help assess their credibility.
Disclaimer
This report details an unverified claim from a dark web forum. Yazoul Security has not independently confirmed the breach of Chronopost Pickup or the authenticity of the data described. The details contained herein-including the scale of the alleged breach, the data types, and the involvement of the threat actor-are based solely on the forum post and should be treated as allegations. The provided file hash is for informational and potential future investigative correlation only. Organizations should seek official channels for confirmation and guidance.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
bbalawgroup.com — safepay
cheeky.com.ar — safepay
firstcambodia.com.kh — safepay
The Epoch Times — coinbasecartel