Fédération Sportive et Gymnique du Travail (FSGT) Breach ...
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
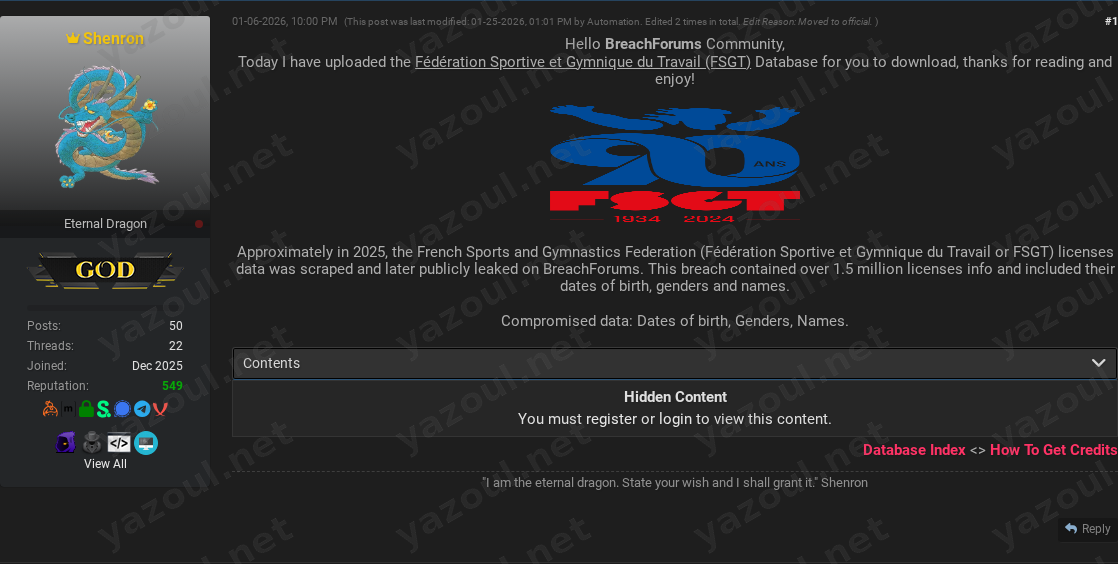
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
An actor using the alias “Shenron” has posted an unverified claim on a dark web forum, alleging the leak of a database belonging to the Fédération Sportive et Gymnique du Travail (FSGT), a French sports and gymnastics federation. The post, dated January 6, 2026, claims the data was scraped in approximately 2025 and contains information on over 1.5 million licenses. The actor has provided a file hash and size details, but no sample data or direct proof of the data’s authenticity is included in the public portion of the post, which is gated behind a forum registration wall.
What Is Allegedly Exposed
According to the threat actor’s post, the compromised dataset purportedly contains 1,560,776 records related to FSGT licenses. The data types allegedly exposed are limited to:
- Names
- Dates of birth
- Genders
The post claims the uncompressed data file is 277.08 MB. An MD5 hash (
0984D7E29CFCDE5A4FFE29EAA59443AF) for a compressed .7z archive is provided, which could theoretically be used for file verification by those who access the download. Notably, the post does not allege the exposure of more sensitive data like physical addresses, contact information, financial details, or passwords.
Threat Actor Profile
The post author, “Shenron,” does not have an established reputation on the forum based on the provided information. The post was edited by an “Automation” account and moved to an “official” section, which may imply some level of curation by forum administrators but does not validate the claim’s truthfulness. The lack of a known reputation for the actor is a significant red flag, as new or unknown actors sometimes post recycled, falsified, or exaggerated data to gain credibility or forum credits.
Potential Impact
If the claim is valid, the exposure of names combined with dates of birth for 1.5 million individuals represents a serious privacy concern. This specific combination of data is a key enabler for identity fraud, targeted phishing campaigns (spear-phishing), and social engineering attacks. Threat actors could use this information to craft highly convincing fraudulent communications or attempt to answer security questions for other accounts. For the FSGT, a confirmed breach could lead to significant reputational damage, regulatory scrutiny under laws like the GDPR, and potential legal liabilities.
What to Watch For
- Verification of Data: The primary indicator will be if independent researchers or journalists can validate the MD5 hash against a circulating file and confirm the data’s authenticity and freshness (i.e., that it is new and not a rehash of old, publicly available information).
- FSGT Response: Monitor for any official statement from the Fédération Sportive et Gymnique du Travail regarding a potential security incident.
- Data Usage: Watch for signs of this data being actively used in phishing kits, spam campaigns, or being sold on other criminal marketplaces, which would suggest it is in active circulation.
- Actor Activity: Observe if “Shenron” posts further details, samples, or makes additional claims, which could help assess credibility.
Disclaimer
This report details an unverified claim from a dark web forum. The alleged data breach has not been confirmed by the Fédération Sportive et Gymnique du Travail (FSGT) or by independent cybersecurity analysts at this time. The information presented is based solely on the threat actor’s post and should be treated as alleged and potentially fabricated. Yazoul Security has not accessed or verified the purported dataset, and the presence of a file hash does not constitute proof of a genuine breach.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
bbalawgroup.com — safepay
cheeky.com.ar — safepay
firstcambodia.com.kh — safepay
The Epoch Times — coinbasecartel