Instagram Expolits (2017-2024): 87k Records Allegedly Leaked
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
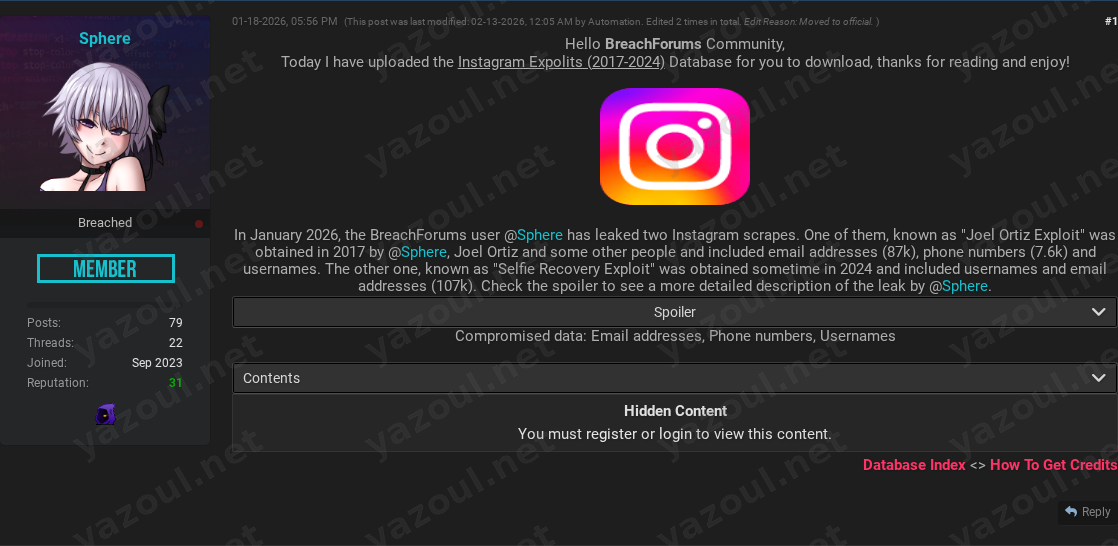
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
A dark web actor using the alias “Sphere” has posted an unverified claim regarding the leak of a database allegedly compiled from two separate Instagram security exploits. The post, made on a breach forum in January 2026, purports to contain data scraped between 2017 and 2024. The threat actor claims the combined dataset includes approximately 87,000 email addresses, 7,600 phone numbers, and associated usernames. The post provides a detailed, technical narrative of how the data was allegedly obtained but offers no direct proof, such as file samples or cryptographic hashes, to substantiate the claim.
What Is Allegedly Exposed
According to the detailed post, the data is said to be sourced from two distinct historical vulnerabilities. The first, dubbed the “Joel Ortiz Exploit,” allegedly dates to August 2017. The claim states that a flaw in Instagram’s password reset process at that time exposed full email addresses and phone numbers instead of partially obscured hints. The actor alleges this was used to scrape data from high-value accounts, including short usernames and celebrity profiles.
The second alleged exploit, referred to as the “Selfie Recovery Exploit,” is claimed to have been active around June 2024. The post describes a convoluted process involving weak password prompts and URL manipulation that purportedly allowed an attacker to bypass authentication and access account recovery information, potentially leading to account takeover. The data types claimed to be exposed across both incidents are email addresses, phone numbers, and Instagram usernames.
Threat Actor Profile
The sole actor mentioned is “Sphere,” who appears to be the author and source of the claimed leak. The post references a historical connection to a person named Joel Ortiz, known from past “sim swap” incidents. However, the credibility of “Sphere” is difficult to assess. The account appears to be actively posting and has taken the step of editing the original post, with a forum “Automation” system moving it to an “official” section-a detail that may imply some level of forum validation but does not verify the data’s authenticity. The lack of a proven track record for significant, verified leaks under this alias is a notable red flag.
Potential Impact
If the claims were true, the exposure of email addresses and phone numbers linked to specific Instagram usernames could facilitate targeted phishing campaigns, credential stuffing attacks, and SIM-swapping attempts. The post specifically alleges that the 2017 data targeted “high value” and celebrity accounts, which could increase the risk of extortion or targeted harassment for affected individuals. The described 2024 exploit also suggests a potential for account takeover, which could lead to identity theft, financial fraud (if linked to business or financial accounts), or reputational damage.
What to Watch For
- Verification Attempts: Monitor for other threat actors discussing or attempting to verify this dataset on other forums or marketplaces. Claims of this nature often see “re-packaging” by other sellers.
- Lack of Proof: The absence of a file hash (MD5 or otherwise) or any sample data is a significant credibility issue. Credible leaks typically include these for verification.
- Exaggerated Narrative: The highly detailed, almost anecdotal description of the exploits, while technical, could be constructed to add a veneer of legitimacy to an otherwise unsubstantiated claim. The mention of a specific celebrity (Selena Gomez) is a common tactic to generate attention.
- Data Freshness: The most recent alleged exploit is claimed to be from 2024. If real, the data could still be relevant, but the two-year gap before the leak claim is unusual and warrants skepticism.
Disclaimer
This report details an unverified claim from a dark web forum. Yazoul Security has not independently confirmed the existence, validity, or scope of this alleged dataset. The details presented are based solely on the threat actor’s post and should be treated as unsubstantiated allegations. The technical descriptions of alleged exploits are provided for contextual understanding of the claim only and do not represent confirmed vulnerabilities. Organizations and individuals should avoid attempting to search for or download any referenced data, as it may be malicious or illegal to possess.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
bbalawgroup.com — safepay
cheeky.com.ar — safepay
firstcambodia.com.kh — safepay
The Epoch Times — coinbasecartel