JobsGo: 2,325,285 records Records Allegedly Leaked
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
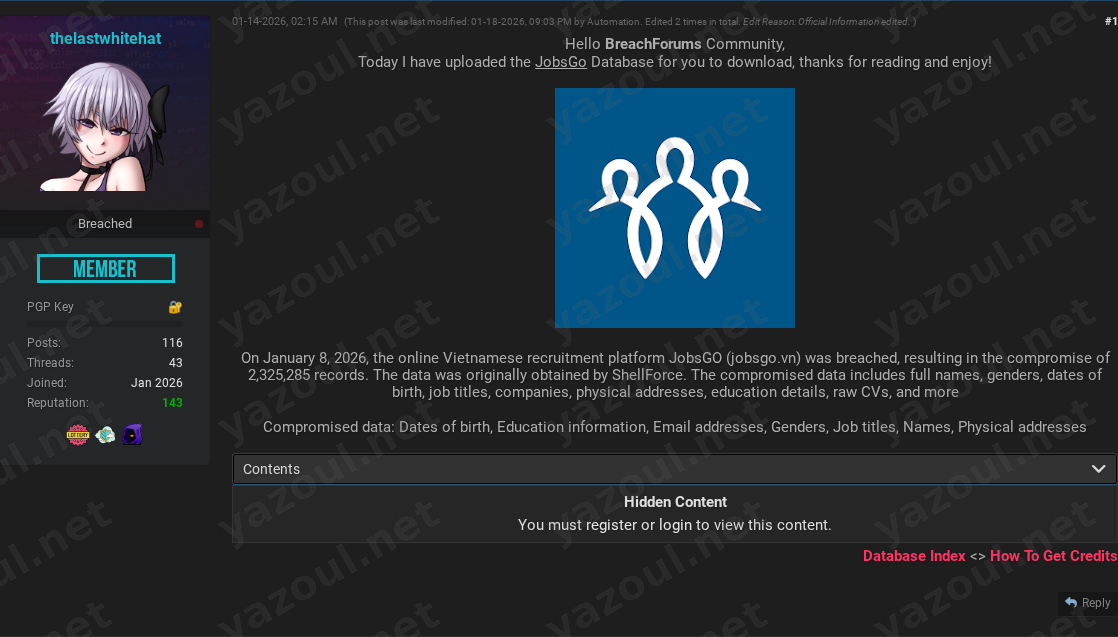
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
A threat actor using the alias “thelastwhitehat” has posted an unverified claim on a dark web forum, alleging a significant data breach of the Vietnamese online recruitment platform JobsGo (jobsgo.vn). According to the post, the breach purportedly occurred on January 8, 2026, and resulted in the compromise of 2,325,285 user records. The actor claims to have uploaded the full database for download by forum members. The post includes a specific MD5 file hash and details on file size, but no sample data or direct proof of the data’s authenticity is publicly visible, as access is gated behind a forum registration wall.
What Is Allegedly Exposed
The threat actor claims the compromised database contains a wide array of sensitive personal and professional information. Allegedly exposed data types include full names, email addresses, physical addresses, dates of birth, and genders. The purported breach also reportedly includes highly sensitive professional details such as job titles, current or past company information, education history, and raw CV documents. The inclusion of raw CVs and physical addresses, if true, would significantly increase the severity of this alleged incident, providing threat actors with material for highly targeted phishing, identity fraud, and social engineering campaigns.
Threat Actor Profile
The post author, “thelastwhitehat,” is not a widely recognized or established threat actor within common intelligence repositories. The post credits another entity, “ShellForce,” as the original source of the data, but no further information about this group is provided. The account’s name and the act of publicly distributing the data for free download are inconsistent with typical “white hat” or ethical security practices, raising immediate credibility concerns. The post was also modified by a forum “Automation” bot, which is a common feature on such platforms and does not lend any legitimacy to the claim itself. The lack of a proven track record for the poster is a significant red flag.
Potential Impact
If the claims are valid, the potential impact on affected individuals is severe. The combination of personal identifiers (date of birth, address) with professional profiles and CVs creates a rich dataset for malicious use. Threat actors could leverage this information for targeted spear-phishing attacks impersonating recruiters or companies, synthetic identity fraud, or direct financial scams. For the organization, JobsGo, a breach of this alleged scale would represent a major crisis, potentially leading to regulatory scrutiny under data protection laws, significant reputational damage, and loss of trust from both job seekers and employers using the platform.
What to Watch For
Organizations and individuals should monitor for corroborating evidence. Key indicators include:
- Corroboration: Watch for other threat actors or sources discussing or selling the same dataset, or for the alleged data appearing on other leak sites.
- Victim Validation: Monitor for any official statement from JobsGo regarding a potential security incident.
- Data Activation: Be alert for a potential increase in targeted phishing campaigns, particularly those mimicking recruitment or HR communications, that may leverage this allegedly stolen data.
- Credential Stuffing: As email addresses are claimed to be part of the leak, there is a risk of credential stuffing attacks against users who reuse passwords on other services.
Disclaimer
This report details an unverified claim from a dark web forum. The information presented here is based solely on the threat actor’s post and has not been independently confirmed by Yazoul Security or corroborated by official sources. The existence, scope, or details of a breach affecting JobsGo have not been verified. The mention of specific data types, record counts, and threat actors reflects only the allegations made in the forum post. This information is provided for situational awareness and defensive intelligence purposes only.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
bbalawgroup.com — safepay
cheeky.com.ar — safepay
firstcambodia.com.kh — safepay
The Epoch Times — coinbasecartel