Maxance: 348k Records Allegedly Leaked
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
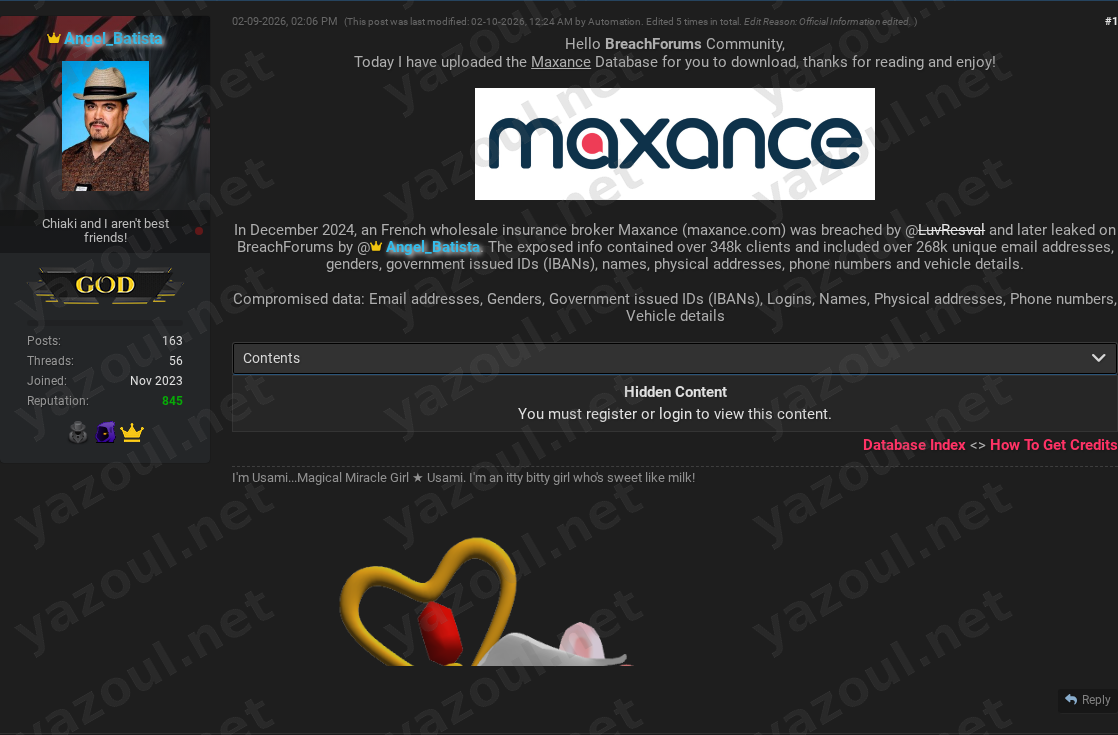
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
A threat actor using the alias “Angel_Batista” has posted an unverified claim on a dark web forum, alleging the breach and leak of a database belonging to Maxance, a French wholesale insurance broker. According to the post, the incident purportedly occurred in December 2024, with the data being leaked in February 2026. The actor claims the database contains approximately 348,345 records related to clients, which were allegedly originally compromised by another individual named “LuvResval.” The post includes a file hash and size details, but no sample data or direct proof of the data’s authenticity has been publicly provided.
What Is Allegedly Exposed
The threat actor claims the compromised database contains a significant volume of sensitive personal and financial information. Allegedly exposed data types include:
- Names
- Email addresses (claimed to be over 268,000 unique addresses)
- Physical addresses
- Phone numbers
- Genders
- Government-issued IDs, specifically International Bank Account Numbers (IBANs)
- Vehicle details
- Login information (the specific nature of these logins is not detailed)
The inclusion of IBANs and physical addresses is particularly concerning, as this combination could facilitate highly targeted phishing, fraud, and identity theft campaigns.
Threat Actor Profile
The post is authored by “Angel_Batista,” an alias with no established reputation or prior history in major leak communities based on this report. The actor credits the initial breach to “LuvResval,” another name that does not correspond to a widely known threat actor in public reporting. The use of relatively unknown aliases is a red flag that warrants skepticism. Furthermore, the forum post shows it was edited five times by an “Automation” script, which could indicate the post is templated or part of a broader spam campaign, rather than a unique, credible disclosure.
Potential Impact
If the claims are valid, the potential impact on the alleged 348,000+ clients is severe. The combination of personal identifiers, contact information, and financial data (IBANs) creates a high-risk scenario for:
- Financial Fraud: IBANs could be targeted for unauthorized transactions or account takeover attempts.
- Targeted Phishing (Spear Phishing): Attackers could craft highly convincing emails or messages using the detailed personal and vehicle information.
- Identity Theft: The breadth of PII exposed is sufficient to attempt identity fraud.
- Secondary Attacks: Login credentials, if included and valid, could be used in credential stuffing attacks against other services.
For the organization, Maxance, such a breach would represent a significant regulatory, reputational, and legal challenge, particularly under strict frameworks like the EU’s GDPR.
What to Watch For
- Verification of Data: Monitor for the alleged data appearing in other forums, ransomware leak sites, or credential stuffing lists. The provided MD5 hash (
C8AAC44C3EC6A8EF6C2B149F5798B90A) could be used by researchers to identify the file elsewhere. - Official Statement: Watch for any public comment or data breach notification from Maxance or relevant French data protection authorities.
- Actor Activity: Observe if “Angel_Batista” or “LuvResval” post further claims or evidence to bolster their credibility.
- Exaggerated Claims: Be cautious of the round numbers and the lack of any data sample. The claim of “over 268k unique email addresses” within a 348k record set is plausible but remains unsubstantiated.
Disclaimer
This report details an unverified claim from a dark web forum. The alleged data breach of Maxance has NOT been independently confirmed by Yazoul Security or corroborated by official sources. All details, including the scope of data, the number of affected individuals, and the involvement of the named threat actors, are based solely on the forum post and should be treated as allegations. The presence of file hashes does not confirm the legitimacy of the data contained within. Organizations and individuals should await official confirmation before taking action based on this report.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
bbalawgroup.com — safepay
cheeky.com.ar — safepay
firstcambodia.com.kh — safepay
The Epoch Times — coinbasecartel