Paris A Coeur Ouvert: 616 records Records Allegedly Leaked
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
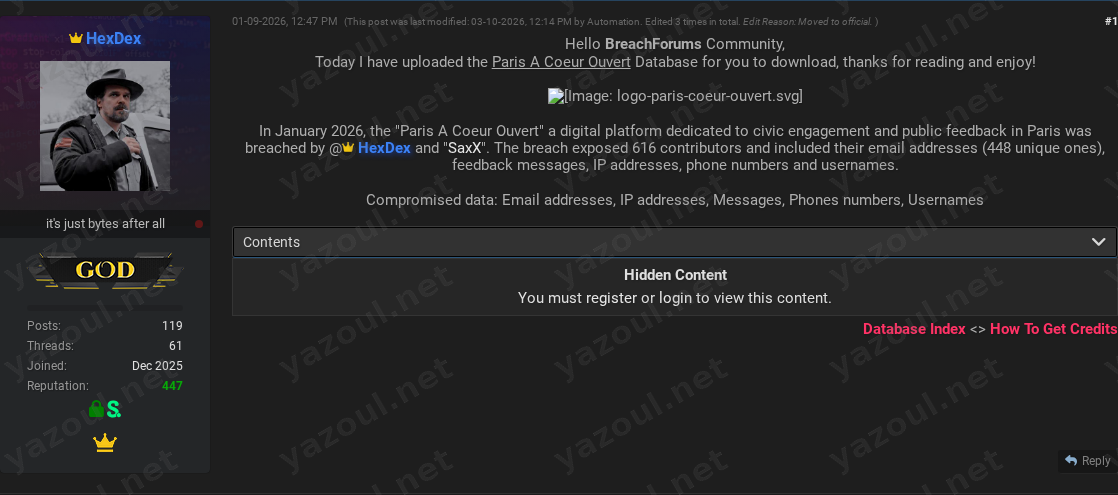
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
An unverified claim has surfaced on a dark web forum alleging a data breach at Paris A Coeur Ouvert, a digital civic engagement platform for Paris. A user posting under the alias “HexDex” published a thread titled “Paris A Coeur Ouvert Database - Leaked, Download!” on January 9, 2026. The post claims that in January 2026, the platform was breached by the poster and another entity referred to as “SaxX,” resulting in the alleged exposure of 616 contributor records. The post includes a file hash and size details, and the data is purportedly being offered for download to registered forum members.
What Is Allegedly Exposed
According to the threat actor’s post, the compromised database allegedly contains 616 records related to platform contributors. The claimed data types include email addresses (with 448 unique addresses specified), usernames, phone numbers, IP addresses, and the feedback messages submitted by users. The personal nature of the data-particularly the combination of contact information, network identifiers (IPs), and the content of personal messages-could be sensitive. The post provides technical details like an MD5 file hash (1DCD731054A2F4212E9EACA31410C45E) and states the uncompressed file size is approximately 538 KB.
Threat Actor Profile
The primary actor named in the post is “HexDex,” who is also the author of the forum thread. The post also references a second entity, “SaxX,” as a co-perpetrator. There is no immediate, widely recognized reputation associated with these aliases in public cybersecurity reporting, which suggests they may be lesser-known or new actors. The post was edited multiple times by an automated forum tool and was moved to an “official” section, which could indicate some level of curation by forum administrators but does not validate the claim’s authenticity. The specificity of the technical details (hash, record count, data types) is a point of note, though it is not conclusive proof.
Potential Impact
If the claim is valid, the potential impact centers on the privacy and security of the 616 alleged victims. The exposure of email addresses and phone numbers could lead to targeted phishing or smishing campaigns. IP addresses could be used for geo-location or network profiling, while the leaked private messages could enable highly personalized social engineering attacks or cause reputational and personal distress. For the organization, Paris A Coeur Ouvert, such a breach could damage public trust in a platform designed for civic engagement and feedback, potentially chilling participation.
What to Watch For
- Verification: Monitor for any official statement from Paris A Coeur Ouvert regarding a potential security incident.
- Data Circulation: Watch for the alleged dataset or parts of it appearing on other forums, leak sites, or in credential-stuffing lists, using the provided MD5 hash for tracking.
- Targeted Campaigns: Be alert for an increase in phishing emails or messages targeting individuals in Paris, potentially referencing civic engagement or feedback topics.
- Actor Activity: Note if the aliases “HexDex” or “SaxX” are linked to other data breach claims in the future, which could help assess their credibility.
Disclaimer
This report details an unverified claim from a dark web forum. The alleged breach and the existence of the data have NOT been independently confirmed by Yazoul Security or, based on available information, by the affected organization. The details presented are solely based on the threat actor’s post and should be treated as unsubstantiated allegations. The provided file hash and technical details are for tracking and investigative purposes only.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
bbalawgroup.com — safepay
cheeky.com.ar — safepay
firstcambodia.com.kh — safepay
The Epoch Times — coinbasecartel