Baydöner: 3.6M Records Allegedly Leaked
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
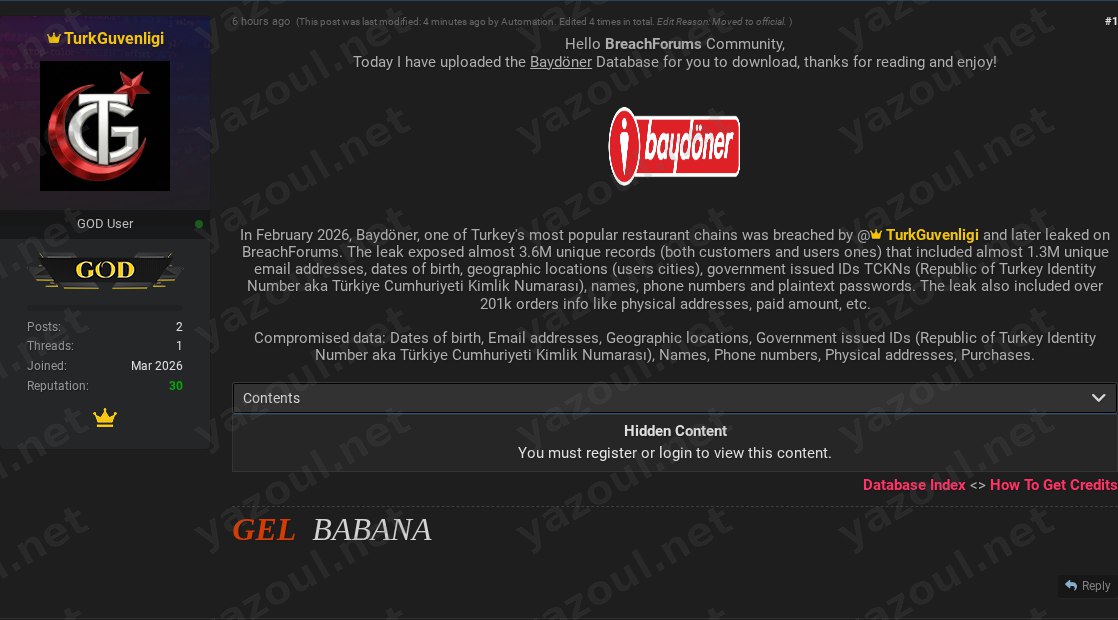
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
An actor using the alias “TurkGuvenligi” has posted on a dark web forum, claiming to have leaked a database allegedly belonging to Baydöner, a popular Turkish restaurant chain. The post, dated March 13, 2026, states the breach occurred in February 2026. The threat actor claims the leak contains approximately 3.6 million unique records, comprising both customer and user data. They have provided a file hash and details on the compressed and uncompressed file sizes, offering the data for download behind a forum registration wall.
What Is Allegedly Exposed
According to the unverified claim, the exposed dataset is extensive and highly sensitive. The threat actor alleges it includes nearly 1.3 million unique email addresses, full names, phone numbers, dates of birth, and geographic location data. Most critically, the post claims the data contains Turkish Republic Identity Numbers (TCKN), which are sensitive government-issued national identifiers. The actor also states that plaintext passwords were exposed, a significant security failure if true. Furthermore, the leak purportedly includes over 201,000 purchase records containing physical delivery addresses, order details, and payment amounts. The combination of national ID numbers, contact information, and financial purchase history would represent a severe compromise of personal data.
Threat Actor Profile
The post is authored by “TurkGuvenligi,” a handle that translates to “Turkish Security.” The actor claims responsibility for both the breach and the subsequent leak. There is no widely recognized reputation or history associated with this specific alias on major English-language forums, which raises immediate questions about credibility. The act of posting the data on a public forum for download suggests motivations that could range from notoriety-seeking to hacktivism, though no explicit motive is stated. The new or unknown nature of the actor is a red flag, often associated with exaggerated claims or re-posted old data.
Potential Impact
If the claims are valid, the potential impact on affected individuals is severe. The alleged exposure of TCKN numbers and plaintext passwords creates an immediate and high risk of identity theft, financial fraud, and targeted phishing campaigns. The inclusion of detailed purchase history and physical addresses could facilitate highly convincing spear-phishing attacks or even physical security threats. For the Baydöner organization, such a breach would likely trigger significant regulatory scrutiny under Turkey’s data protection law (KVKK), potentially resulting in heavy fines and severe reputational damage that could impact customer trust and business operations.
What to Watch For
- Official Verification: Monitor for any official statement from Baydöner regarding a potential data security incident. Silence or denial does not disprove the claim, but confirmation would validate it.
- Data Circulation: Watch for the alleged dataset or subsets of it appearing on other hacking forums, Telegram channels, or credential-stuffing lists. The provided MD5 hash (
91125685A1629C6FBC833EA79AF8A1B0) can be used to identify this specific file in other locations. - Credential Stuffing Attacks: An increase in credential stuffing attacks against Baydöner’s online services or reports of account takeovers from customers could be an indirect indicator that the password data is genuine and in use.
- Actor Follow-up: Note if “TurkGuvenligi” posts further evidence, makes demands, or claims other breaches, which could help assess their credibility.
Disclaimer
This report details unverified claims from a dark web forum. Yazoul Security has not independently confirmed the breach of Baydöner or the validity of the allegedly leaked data. The details presented, including the scale of the breach and the types of data exposed, are solely based on the threat actor’s post. The provided file hash and technical details do not constitute proof that the data is genuine or originates from the named organization. All claims should be treated as alleged until corroborated by credible evidence or an official statement.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
bbalawgroup.com — safepay
cheeky.com.ar — safepay
firstcambodia.com.kh — safepay
The Epoch Times — coinbasecartel