BreachForums new ownership + takedown (March 2026)
Unverified dark web claim. This report is based on a post observed on a dark web forum. Yazoul Security has not independently verified the authenticity of this claim.
Leak Site Screenshot
Screenshot captured at time of discovery. Sensitive data has been redacted.
Claim Summary
On March 16, 2026, two major events converged to take BreachForums — one of the most prominent English-language dark web forums for trading stolen data — offline.
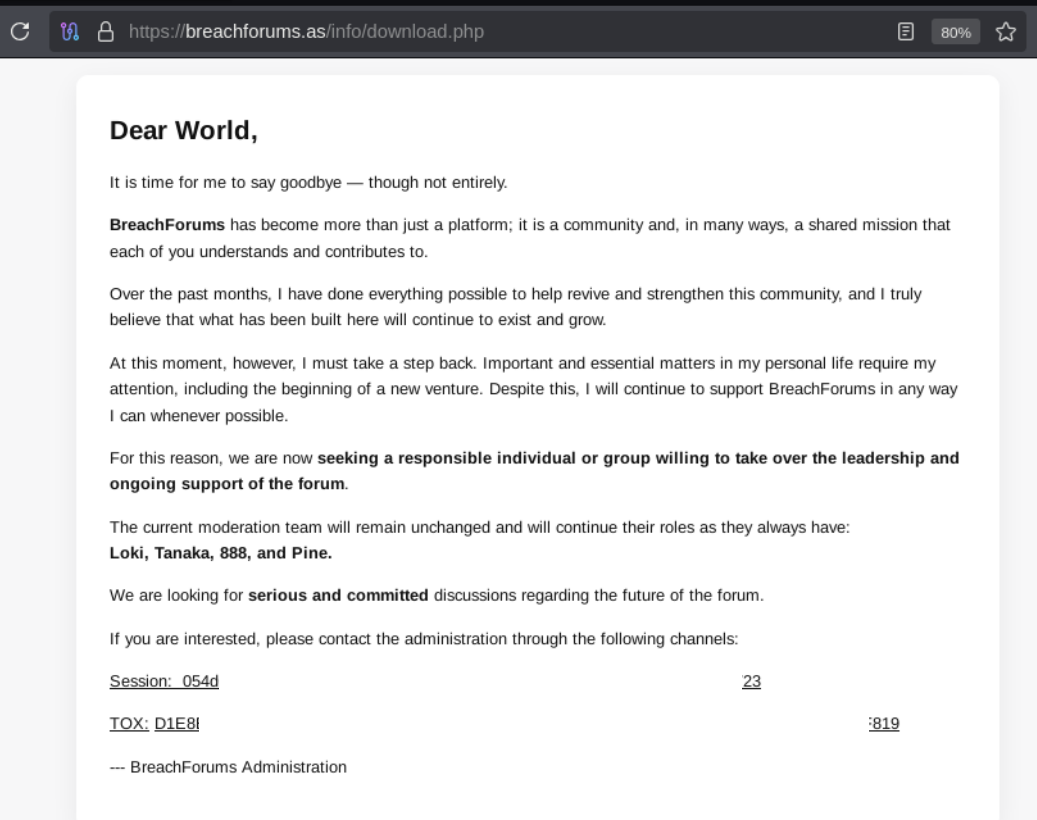
First, the forum’s administration published a farewell message on the domain breachforums[.]as, announcing that the current administrator is stepping back from leadership and that the forum is actively seeking a new individual or group to take over ownership.
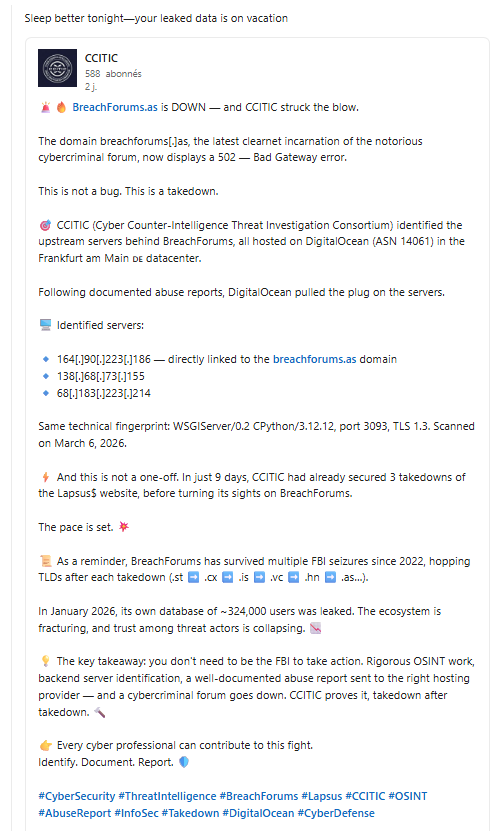
Shortly after, CCITIC (Cyber Counter-Intelligence Threat Investigation Consortium) announced via LinkedIn that they had identified the upstream servers behind the clearnet domain and successfully coordinated their takedown through abuse reports to the hosting provider. The domain breachforums[.]as now returns a 502 Bad Gateway error.
This double blow — a leadership vacuum combined with an infrastructure takedown — marks a significant inflection point for one of the most active data leak marketplaces in the cybercrime ecosystem.
Key Details from the Announcement
The public statement, posted at breachforums[.]as/info/download.php, includes the following key points:
- The current administrator is stepping down from day-to-day leadership, citing personal matters and a new venture.
- The moderation team remains intact. Four moderators — Loki, Tanaka, 888, and Pine — will continue in their roles during the transition.
- New leadership is being sought. The administration is looking for “a responsible individual or group” to assume control of the forum.
- Contact channels for interested parties were provided via Session and TOX encrypted messaging platforms — both commonly used in cybercriminal circles for their strong anonymity guarantees.
Notably, the message frames BreachForums as a “community” and “shared mission,” indicating the administrator views the platform as more than a marketplace and hopes it will continue to operate under new management.
CCITIC Takedown: Server Identification and Abuse Reports
On the same day, CCITIC (Cyber Counter-Intelligence Threat Investigation Consortium) publicly claimed responsibility for taking down the clearnet infrastructure of BreachForums. According to their LinkedIn post, CCITIC conducted OSINT-based reconnaissance and identified the backend servers powering breachforums[.]as.
Identified Infrastructure
All servers were hosted on DigitalOcean (ASN 14061) in the Frankfurt am Main, Germany datacenter:
164[.]90[.]223[.]186— directly linked to thebreachforums[.]asdomain138[.]68[.]73[.]15568[.]183[.]223[.]214
The servers shared a common technical fingerprint: WSGIServer/0.2 CPython/3.12.12, running on port 3093 with TLS 1.3. CCITIC states the scanning was performed on March 6, 2026 — ten days before the public announcement.
Takedown Method
CCITIC reports that following documented abuse reports submitted to DigitalOcean, the hosting provider terminated the servers. The domain breachforums[.]as subsequently began returning a 502 Bad Gateway error, confirming the infrastructure was pulled.
CCITIC Track Record
CCITIC claims this is not an isolated action. The group states they had already secured 3 takedowns of the Lapsus$ website in the 9 days prior to targeting BreachForums. Their approach relies on OSINT techniques — backend server identification, technical fingerprinting, and documented abuse reports to hosting providers — rather than law enforcement coordination.
Timing Considerations
The proximity of the administration’s farewell announcement and the CCITIC takedown raises questions about whether these events are related:
- Coincidence: The administrator may have been unaware of CCITIC’s activities and the timing is coincidental.
- Awareness of pressure: The administrator may have been aware of ongoing takedown efforts or other external pressure, accelerating the decision to step back.
- Preemptive move: The farewell letter could represent a strategic attempt to hand off leadership before infrastructure became untenable.
Yazoul Security has not independently verified CCITIC’s claims or the causal relationship between their actions and the forum going offline.
Historical Context
BreachForums has a turbulent history of leadership changes and law enforcement actions:
- 2022: RaidForums is seized by the FBI; Pompompurin (Conor Brian Fitzpatrick) launches BreachForums as its successor.
- March 2023: Pompompurin is arrested by the FBI at his home in Peekskill, New York.
- 2023–2024: ShinyHunters takes over administration. The forum is seized and relaunched multiple times across different domains.
- 2024–2026: The forum resurfaces under new administration, migrating through multiple TLDs:
.st→.cx→.is→.vc→.hn→.as. - January 2026: BreachForums’ own database of approximately 324,000 user records is leaked, further eroding trust within the community.
- March 2026: Administration announces leadership transition; CCITIC claims server takedown via DigitalOcean abuse reports.
Each leadership transition has historically created periods of instability, trust erosion, and migration of users to competing platforms. The combination of the January 2026 database leak, the leadership exit, and the CCITIC takedown suggests the ecosystem around BreachForums is fracturing at an accelerated pace.
Implications for the Threat Landscape
This leadership vacuum carries several implications for the cybersecurity community:
- Short-term disruption: With infrastructure down and no active leadership, forum activity and data trading are effectively halted.
- OSINT-driven takedowns as a model: CCITIC’s approach — identifying backend servers via scanning and filing abuse reports with hosting providers — demonstrates that cybercriminal infrastructure can be disrupted without law enforcement involvement. This could inspire similar community-driven efforts.
- Potential law enforcement angle: Previous BreachForums leadership transitions have coincided with or been precipitated by law enforcement operations. While the announcement frames this as a voluntary departure, the timing and language should be scrutinized.
- Ecosystem fragmentation: With the forum offline and trust eroded by the January 2026 database leak, users may scatter to competing platforms such as Exposed, LeakBase, or Telegram-based data trading channels, further fragmenting the dark web data market.
- Infrastructure resilience question: BreachForums has historically recovered from FBI seizures by migrating TLDs. However, an abuse-report-based takedown targeting the actual hosting provider is a different vector — it targets infrastructure rather than domain names, potentially making recovery harder.
- Operational security risk for users: Leadership transitions are historically exploited by law enforcement to insert informants or compromise forum infrastructure. The 324,000-user database leak compounds this risk.
What to Watch For
- New domain or infrastructure migration: BreachForums has survived multiple seizures by hopping TLDs. Monitor for a new domain emerging (the next TLD after
.as), potentially with hosting moved away from major cloud providers to more bulletproof infrastructure. - New administrator announcement: Monitor for any public statement introducing a successor. The identity, reputation, and operational security posture of new leadership will determine the forum’s trajectory.
- CCITIC follow-up actions: CCITIC has demonstrated a pattern of repeated takedowns (3 Lapsus$ takedowns in 9 days). They may continue targeting BreachForums infrastructure if it resurfaces.
- Law enforcement activity: Watch for any related arrests, indictments, or seizure banners — previous leadership transitions have been linked to law enforcement operations.
- User migration patterns: Track whether major threat actors and data vendors begin listing on alternative platforms, which would indicate a loss of confidence in BreachForums’ continuity.
- DigitalOcean response: The fact that BreachForums was hosted on a mainstream cloud provider (DigitalOcean) rather than bulletproof hosting is notable. Future iterations may move to more resilient infrastructure.
References
Disclaimer
This report is based on a publicly accessible announcement posted by the BreachForums administration and a public LinkedIn post by CCITIC. Yazoul Security has not independently verified the motivations behind the leadership transition, CCITIC’s claimed role in the takedown, or the causal relationship between the two events. The server IPs and technical details cited are sourced from CCITIC’s public claims and have not been independently confirmed. This intelligence is provided for situational awareness and defensive security purposes only.
CTI Research? Separate Your Traffic
Investigating dark web forums, threat actor infrastructure, or malware C2 panels? A VPN isolates your research traffic from your corporate IP. Layer it under Tor or route your sandbox egress through it for clean attribution separation.
Get NordVPN for CTIAffiliate link — we may earn a commission at no extra cost to you.
Never miss a threat intelligence alert
Get real-time security alerts delivered to your preferred platform.
Related Claims
bbalawgroup.com — safepay
cheeky.com.ar — safepay
firstcambodia.com.kh — safepay
The Epoch Times — coinbasecartel